Identity Security Posture Management
Know your identity security posture at all times
Linx continuously monitors your entire identity environment — mapping risks, enforcing policies, and maintaining an accurate view of your identity security posture across every identity type. So when something changes, Linx knows.
.webp)
.webp)
.webp)
Built for and trusted by leading enterprises



















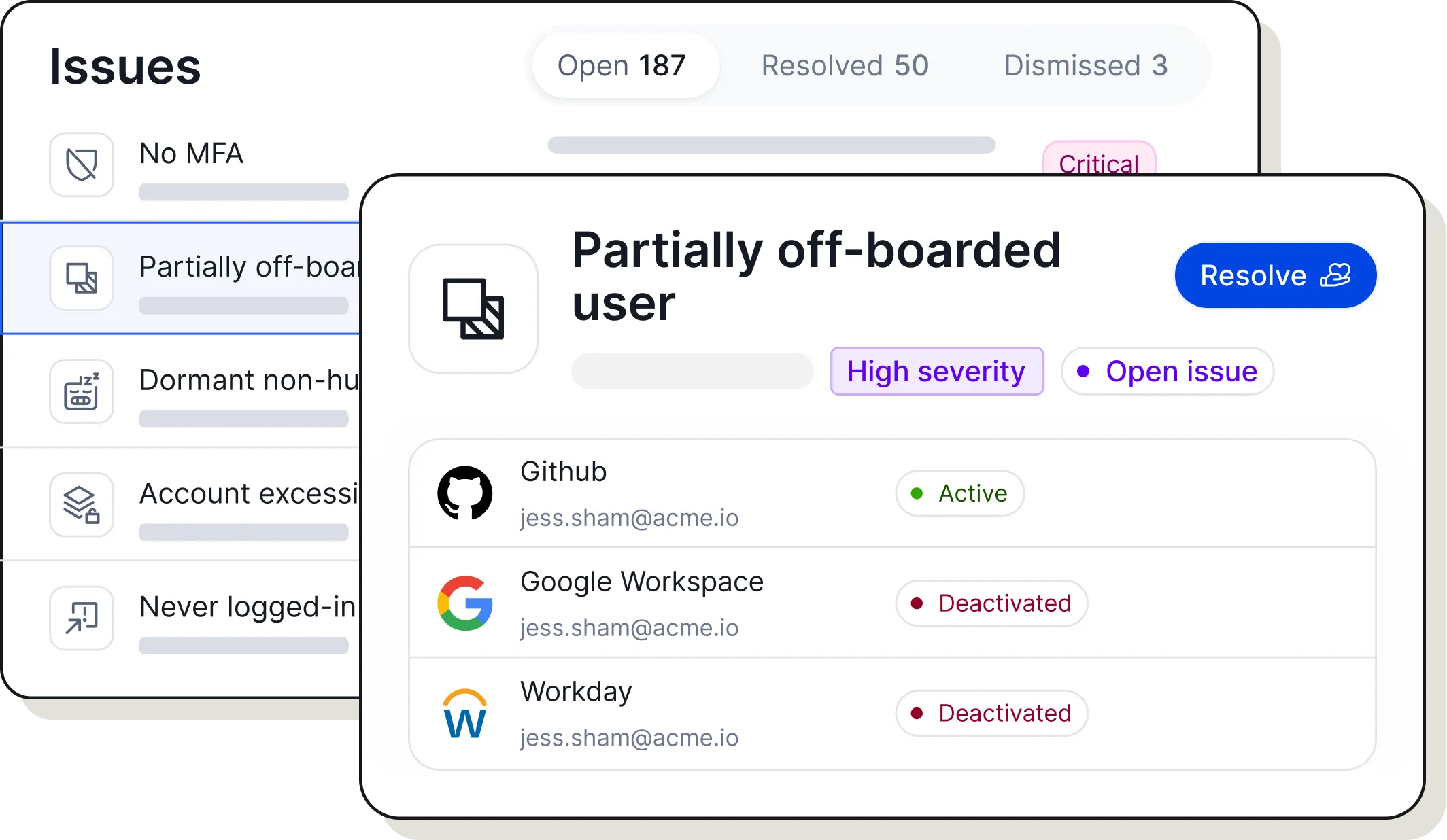
A continuous, comprehensive view of identity risk across your enterprise
Most identity tools show you problems. Few help you fix them. Linx closes the loop: discover what access exists, understand why it is risky, and remediate directly in the platform.
Unified visibility into the identity attack surface
One Graph shows all identities, all access, and every risk. The Graph leaves no blind spots by correlating data from your cloud, SaaS, on-prem and home grown systems into a single, normalized view.

Risk detection and analytics
Detect dormant accounts, excessive privileges, weak authentication, orphan accounts, exposed credentials, and hidden identity-based attack vectors that malicious actors could exploit.

Proactive remediation
Prioritize and resolve identity-based risks based on identity context and automatically remediate identity risks with identity-centric workflows.
“Linx is revolutionizing the identity security and governance space. Legacy IGA can be overwhelming in both cost and effort resulting in diminishing or even negative ROI.“