Identity Intelligence & Analytics
Understand what your access data is actually telling you


















Turn your identity graph into decisions, not dashboards
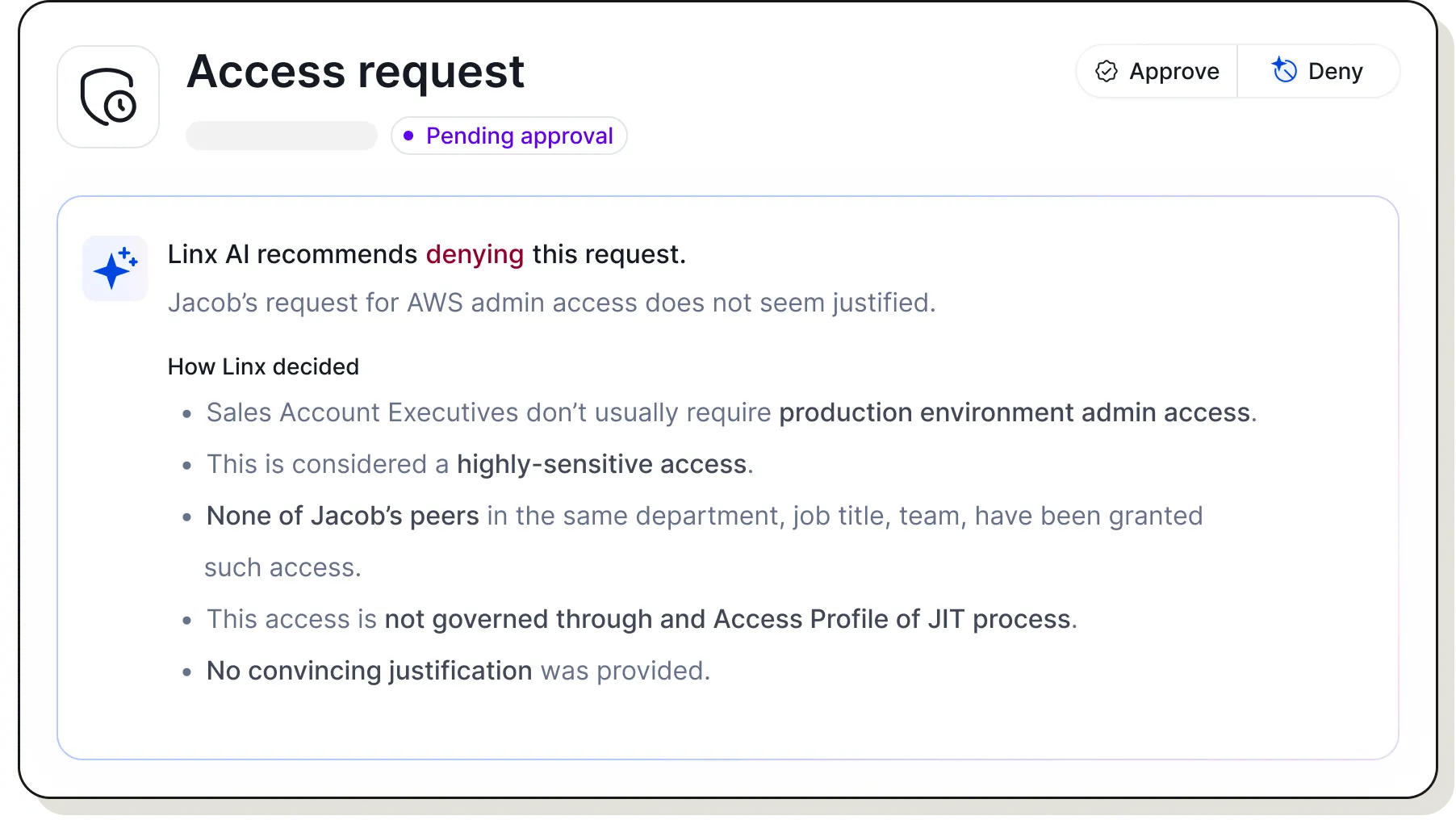
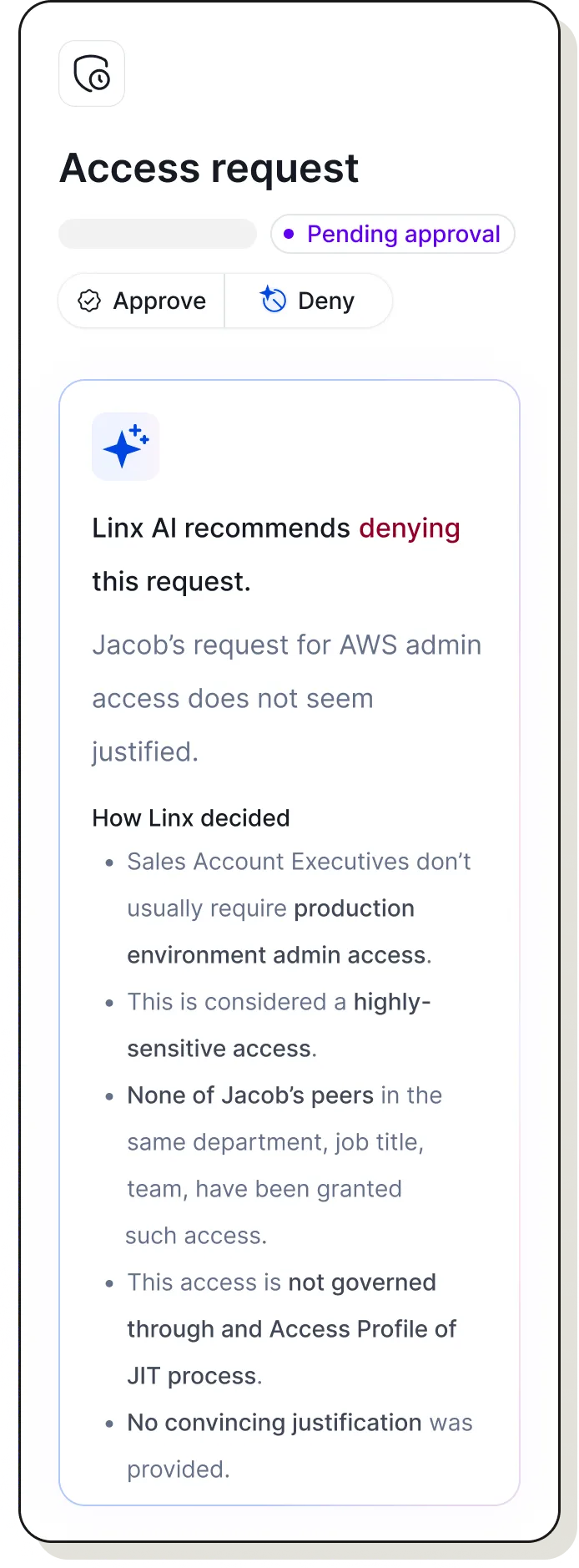
Privilege analysis & blast radius
Linx classifies every entitlement in your environment, identifying administrative and highly privileged accounts and whether privilege was explicitly granted or quietly accumulated over time. It then maps each identity's full access blast radius: the complete scope of what an attacker could reach if that account were compromised.

Peer & usage analysis
Linx compares access across identities in similar roles, departments, and teams — flagging identities whose entitlements are significant outliers from their peers. It then layers in usage data, distinguishing between access people actually use and access that sits dormant. Together, these two signals identify the excessive, stale, and unjustified entitlements that represent standing risk with no business justification.

Semantic analysis
Linx cross-references job titles, roles, departments, and responsibilities to evaluate whether an identity's access actually makes sense — and flags the mismatches that policy alone would never catch.

“Linx is revolutionizing the identity security and governance space. Legacy IGA can be overwhelming in both cost and effort resulting in diminishing or even negative ROI.“