Identity Policy Enforcement
Define your guardrails. Enforce them automatically.
Policies without enforcement are just documentation
Most organizations have identity policies, but few enforce them. Linx turns policies into automated controls and flags drift before auditors do.
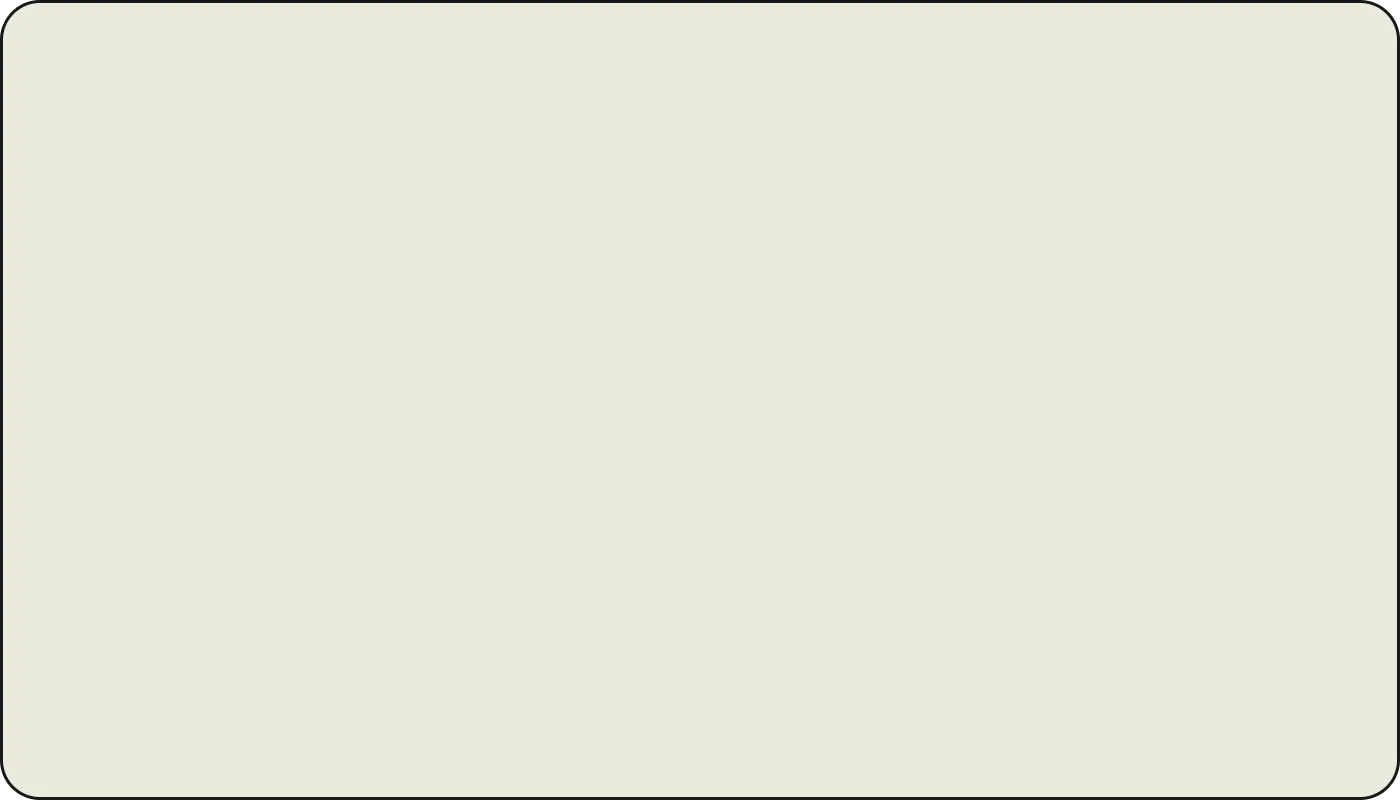
Access Request Policies With Built-In Controls
- Self-service access is only safe when governed by policy. Linx lets you define who can request what, for how long, and who approves.
- Requests route automatically based on your rules: manager, app owner, or auto-approval for low-risk entitlements.
- Access is provisioned when approved and gets revoked automatically when the window closes.
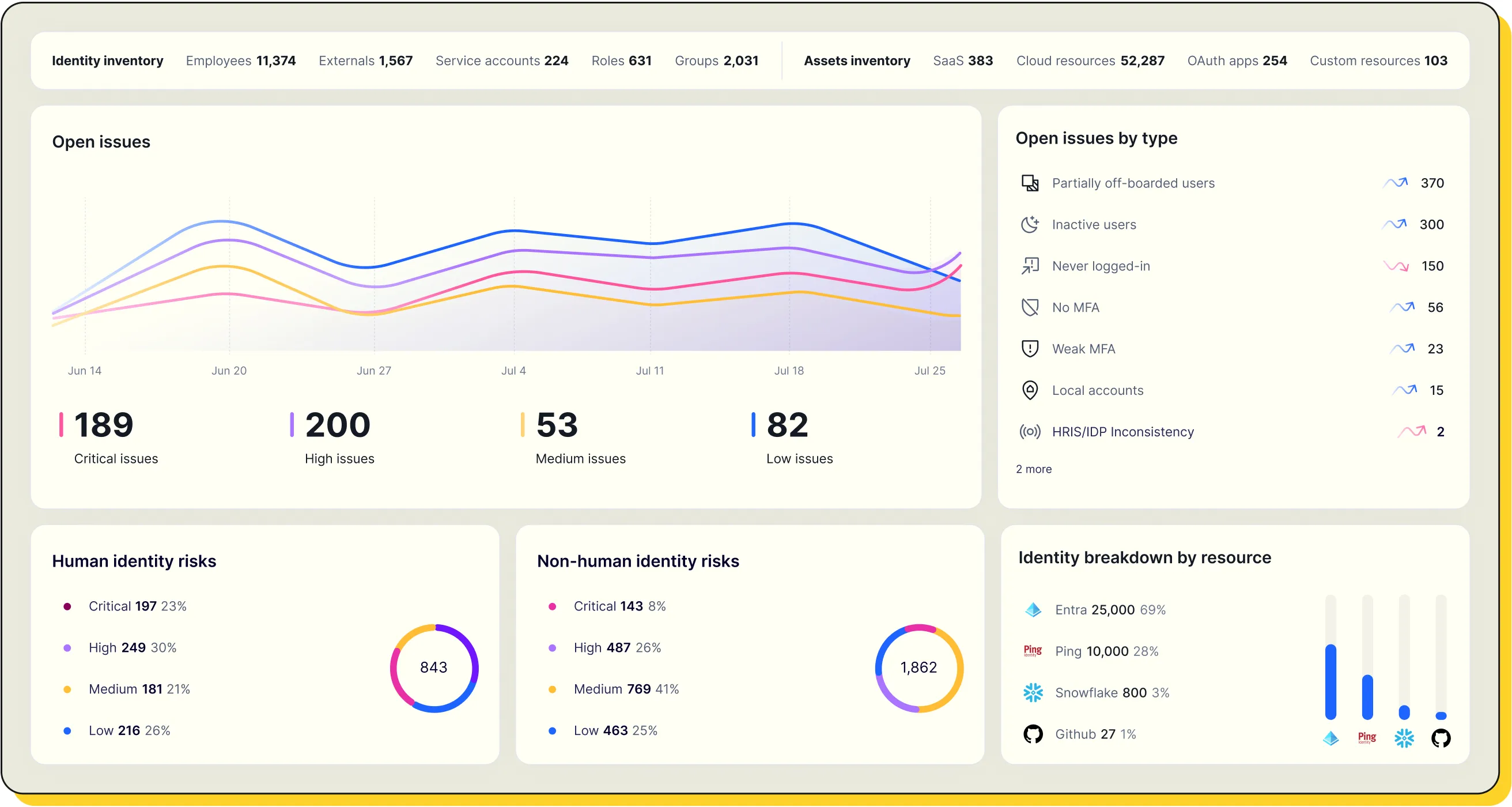
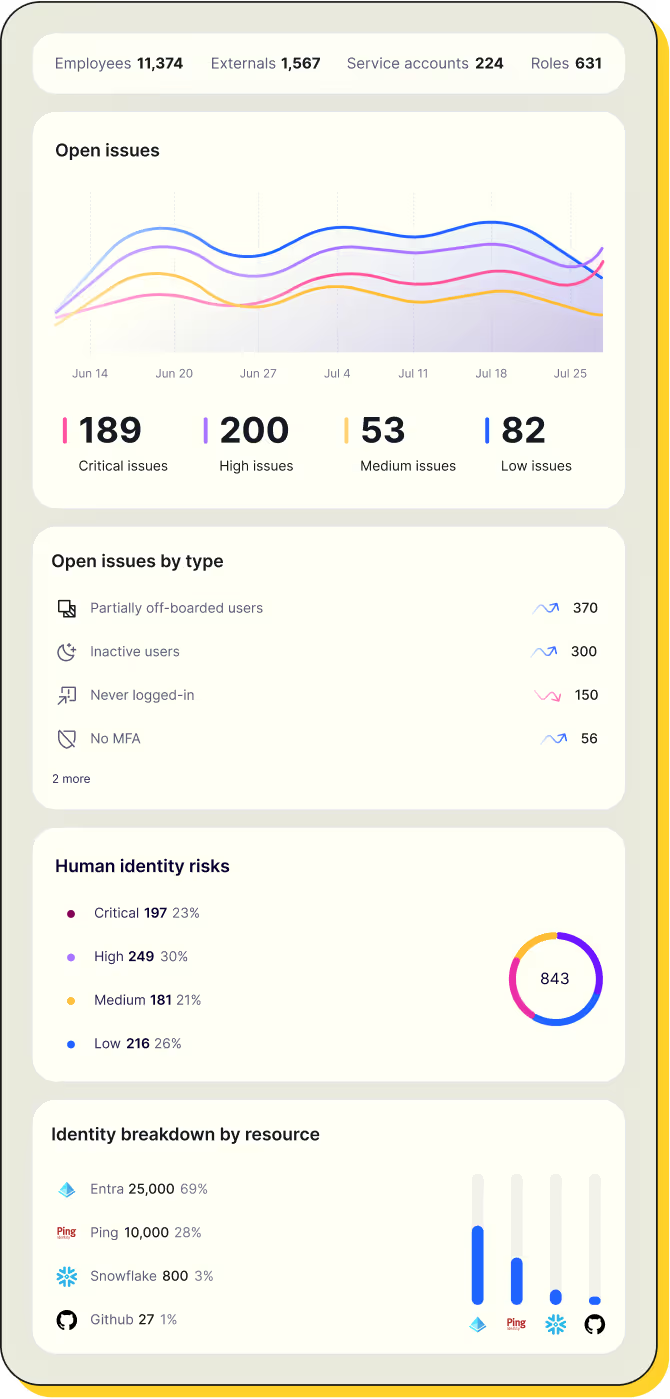
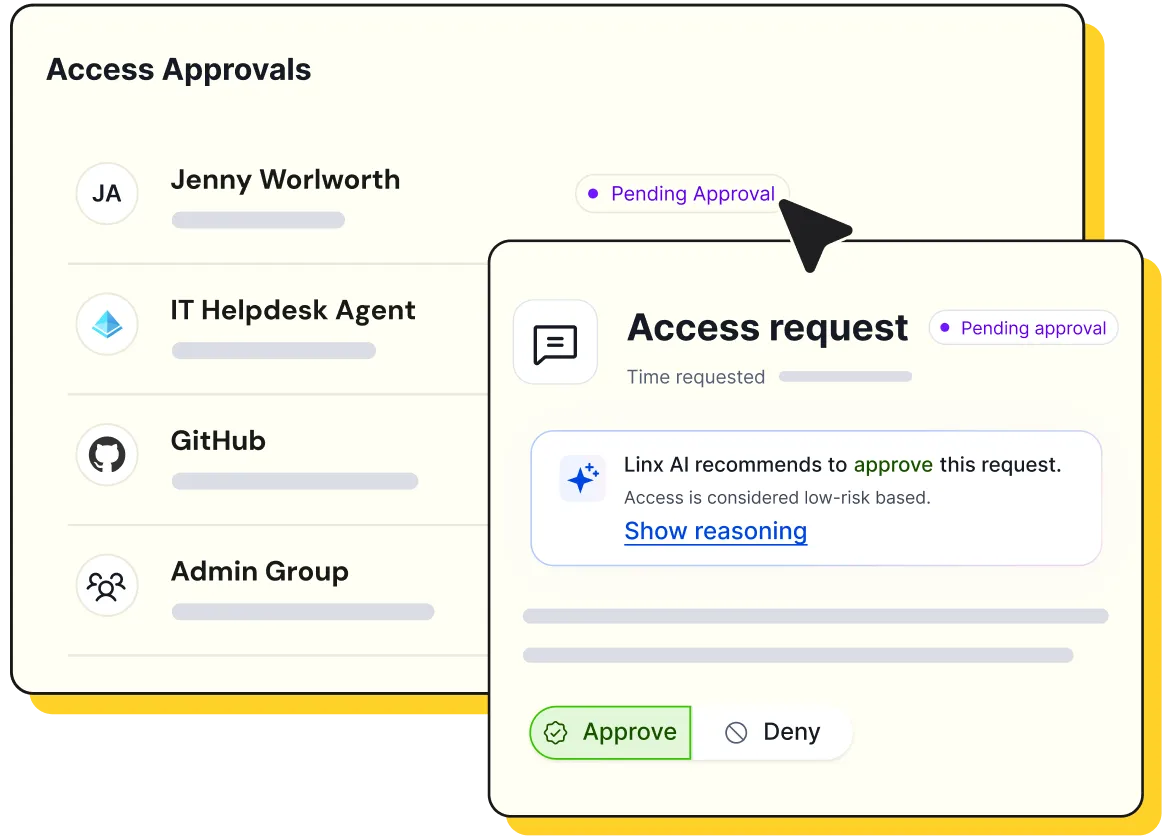
Continuous Monitoring for Policy Drift
- Policies enforced once and forgotten will drift. Linx monitors your environment continuously for new violations, whether they come from manual changes, provisioning errors, or access that accumulated over time.
- When something falls outside policy, you know about it before your next audit cycle, not during.
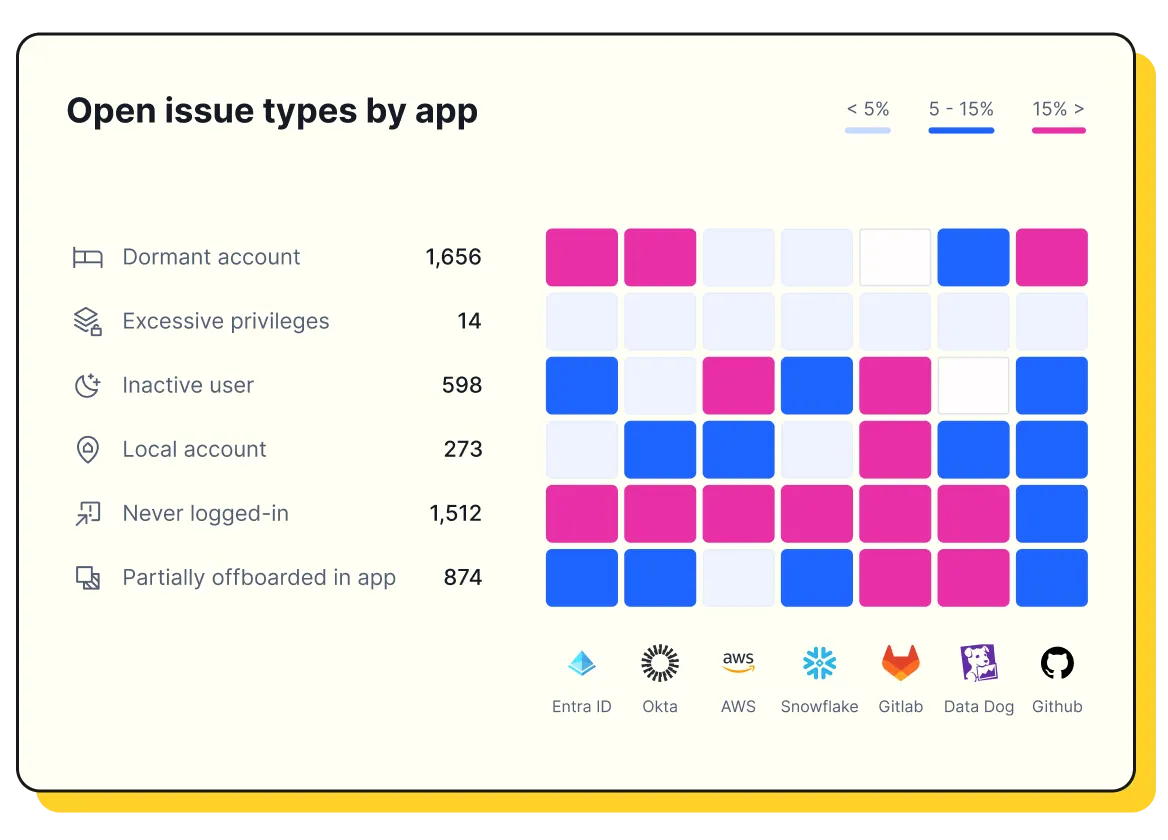
Segregation of Duties That Actually Gets Enforced
- Conflicting access is a compliance problem and a security risk. Linx lets you define SoD across your connected systems.
- The platform continuously monitors for violations, shows who holds conflicting access, and lets you resolve issues by removing the offending entitlement.
- Acceptable exceptions can be documented and tracked without losing visibility.
Audit-Ready Evidence Without the Scramble
- Every policy decision, violation, remediation, and exception is logged.
- When auditors ask how you enforce least privilege or segregation of duties, you can show them the policy, the monitoring, and the evidence that violations were addressed.
- Compliance becomes a byproduct of how you operate, not a quarterly fire drill.

.webp)
