Linx Team
Linx Team
The Linx team is on a mission to redefine identity security for the modern enterprise. We're a group of security practitioners, engineers, and builders working on an AI-native platform that maps, monitors, and governs every identity — human, non-human, and agentic. Here, we share what we're learning about identity, governance, and the future of secure access.

Articles by
Linx Team
From reactive and manual to proactive, intelligent, and automated.
At Linx Security, our mission is to make identity governance and administration both radically intelligent and radically autonomous. That mission just took a major leap forward.
Earlier this year, we introduced the Linx AI-assistant - a powerful natural language interface that lets anyone ask complex identity questions and get clear, actionable answers without writing a single query.
Today, we’re taking the next step forward.
We are excited to announce the Linx MCP Server - a powerful new runtime service that unlocks seamless interactions between large language models (LLMs) and your identity security and governance data. This is more than just a backend update: it's a strategic foundation that transforms the Linx Platform into a truly agentic system - where intelligent agents don’t just observe your environment, they understand, reason, and act.
What is MCP, and why does it matter?
The Model Context Protocol (MCP) is rapidly becoming the standard for connecting AI models to enterprise systems. Originally introduced to bridge the gap between LLMs and external tools, MCP enables structured, secure communication between AI agents and real-world applications, APIs, and databases.
But while others have used MCP to enrich general-purpose agents, Linx is the first to bring it deeply into the heart of Identity Security and Governance.
Our new MCP Server externalizes three powerful capabilities of the Linx Platform:
Deep graph-based visibility, insights and intelligence: Let agents ask and query the Linx Identity Graph to answer any question on the identity data.
- Unified Identity Security and Governance: Give AI agents safe, governed access to sensitive identity actions like human and non-human Identity investigation, risk detection, as well as access profile, JIT access request, and Access Certification.
- Automation and Remediation at Scale: Let agents flag, recommend, or even trigger the cleanup of unused, risky, or unapproved access, as well as secure identity lifecycle management and access governance.
Built for the Agentic Ecosystem
The Linx MCP Server is designed to plug directly into the rapidly expanding world of AI agents. It’s already integrated with the Linx AI-assistant, and now, it allows you to effortlessly set bi-directional integrations with third-party agents like ChatGPT, Claude, and Gemini.
That means your favorite AI copilots can:
- Investigate and remediate human and non-human identity risks more quickly.
- Onboard and off board new employees and ensure they get exactly the access they need.
- Connect to ticketing systems to automate the processing of access requests.
- Get user inputs and send user notification in your messaging solutions.
- Streamline compliance with contextual recommendations and take action when needed.
We're not just making identity security and governance searchable and actionable, we are making it continuous and autonomous.
Start Your Agentic Governance and Security Journey Today
Don't let a lack of personnel slow you down! With Linx MCP, you can automate your processes without running a single line of code. Whether you're removing access to overprivileged accounts or driving a User Access Review campaign to completion, it's never been easier to secure and govern identity.
Try it now and experience how effortlessly you can empower your team and boost your IAM program with an AI-native Identity Security and Governance Platform. Schedule a demo to start your journey toward an agentic identity security and governance program today!
Holiday Access Risks: Managing Identity Security During the Holiday Season
The holiday season brings unique challenges for enterprises. While employees take time off, cybercriminals ramp up their efforts, targeting organizations during periods of reduced staffing and increased operational flexibility. For identity and access management (IAM) teams, this period requires heightened vigilance.
At Linx Security, we’ve observed that holiday periods often lead to an uptick in security incidents linked to access mismanagement. From rushed access approvals to inactive accounts being exploited, the risks are significant—but they can be mitigated with the right strategies. Here’s how enterprises can stay secure while embracing the holiday spirit.
1. Increased Third-Party Access During the Holidays
The Risk:
During the holiday season, many enterprises rely on contractors, temporary staff, or third-party vendors to maintain operations. These third parties often require access to critical systems, yet their onboarding and offboarding processes are frequently rushed or incomplete.
A Ponemon Institute study revealed that 59% of organizations experienced a data breach due to third-party access mismanagement. Implementing stricter controls during high-risk periods like the holidays is essential.
Actionable Strategy:
- Automate Onboarding and Offboarding: Use IAM tools to streamline and enforce consistent processes for third-party access.
- Set Temporary Access Windows: Limit access duration to the holiday period, ensuring credentials expire automatically.
- Monitor Third-Party Behavior: Continuously track and analyze activity from third-party accounts to detect anomalies.
2. Reduced Staffing and Security Oversight
The Risk:
Reduced staffing during holidays often leads to delayed threat detection and response times. Attackers exploit these gaps, knowing incident response teams are operating with skeleton crews.
According to Cybersecurity Dive, security incidents spike by 30% during major holidays. Having automated systems in place ensures you’re not reliant solely on human intervention.
Actionable Strategy:
- Implement ITDR Solutions: Identity Threat Detection and Response (ITDR) tools can automate threat detection and take preemptive actions, such as locking compromised accounts.
- Set Up Holiday-Specific Policies: Configure your IAM platform to enforce stricter authentication requirements during off-hours.
- Leverage AI for Continuous Monitoring: Use AI-driven tools to identify unusual access patterns, such as logins from new geolocations or at odd hours.
3. Temporary Role Changes and Privilege Escalations
The Risk:
Holiday schedules often lead to role changes, such as managers temporarily delegating access rights to team members. This increases the risk of privilege creep and misuse.
In a 2023 report, Forrester emphasized the importance of JIT access as a zero-trust best practice, particularly during periods of organizational disruption.
Actionable Strategy:
- Enforce Just-in-Time (JIT) Access: Use JIT provisioning to grant temporary elevated privileges that automatically revoke after a set period.
- Audit Privilege Escalations: Regularly review changes to access permissions during the holiday season.
- Use Adaptive MFA: Add extra layers of security for accounts with newly escalated privileges.
4. Stale and Inactive Accounts
The Risk:
Inactive accounts, such as those of employees on extended holiday leave, are prime targets for attackers. These accounts often go unnoticed during routine security checks.
Gartner estimates that 30% of breaches are linked to inactive or orphaned accounts. Proactively addressing these risks during the holidays can prevent exploitation.
Actionable Strategy:
- Suspend Unused Accounts: Temporarily disable accounts for employees on extended leave.
- Automate Dormant Account Detection: Use your IAM platform to flag accounts that haven’t been used within a set time frame.
- Audit Orphaned Accounts: Ensure no accounts are tied to departed employees or contractors.
5. Increased Remote Work Risks
The Risk:
Many employees work remotely during the holidays, often from unsecured personal devices or public networks. This creates vulnerabilities, particularly when accessing sensitive systems.
A 2024 report by CSO Online found that 75% of organizations experienced a surge in remote work-related security incidents during the holidays. Strengthening remote access policies is a critical defense.
Actionable Strategy:
- Enforce Device Trust Policies: Require that only pre-approved and compliant devices can access enterprise systems.
- Deploy Adaptive Access Controls: Use geolocation, device type, and behavioral patterns to adjust authentication requirements dynamically.
- Educate Employees: Run holiday-specific security awareness campaigns, reminding staff about secure access practices.
6. Phishing Campaigns Targeting Holiday Chaos
The Risk:
Cybercriminals exploit the holiday rush with targeted phishing campaigns. Emails disguised as holiday deals, time-sensitive HR notices, or even fake holiday greetings can trick employees into revealing credentials.
The Anti-Phishing Working Group (APWG) reported a 38% increase in phishing attacks during the 2023 holiday season. Proactive training and strong IAM measures can mitigate these risks.
Actionable Strategy:
- Implement Email Filtering: Use advanced email security tools to block suspicious messages before they reach employees.
- Enforce MFA Across All Accounts: Ensure compromised credentials cannot be used without secondary authentication.
- Conduct Simulated Phishing Tests: Run holiday-themed phishing tests to raise awareness among employees.
7. Ensuring Business Continuity
The Risk:
While securing systems is a top priority, excessive restrictions can hinder productivity and disrupt holiday operations.
Balancing security with usability ensures operations continue smoothly while maintaining robust defenses.
Actionable Strategy:
- Implement Role-Based Access Controls (RBAC): Ensure employees only have access to the tools they need, reducing unnecessary friction.
- Create a Holiday Access Playbook: Define clear protocols for granting, revoking, and monitoring access during the holiday season.
- Monitor in Real Time: Use IAM platforms with real-time dashboards to track access activities without delays.
Conclusion: Staying Secure Without Sacrificing Holiday Spirit
The holiday season doesn’t have to be a time of heightened risk for enterprises. With proactive planning, robust IAM practices, and the right tools, organizations can navigate this challenging period securely. At Linx Security, we specialize in helping enterprises implement adaptive, scalable IAM and Modern IGA solutions that minimize risks and enhance operational resilience.
As the holidays approach, now is the time to evaluate your IAM strategy. Are your systems prepared for the unique challenges of this season?
Stay ahead of holiday access risks with Linx Security. Contact us or explore how our IAM solutions can safeguard your enterprise during the busiest time of the year.
Identity and Access Management (IAM) was a cornerstone of cybersecurity in 2024, reflecting its critical role in protecting hybrid environments, securing digital transformation, and mitigating sophisticated threats. This year highlighted the importance of IAM not just as a technical discipline but as a strategic enabler of resilience and compliance.
Drawing on our expertise at Linx Security, we’ve outlined the most important IAM trends of 2024 and how they will shape 2025. Each trend is accompanied by actionable insights to help enterprises position themselves for success in the coming year.
1. Unified Identity Platforms Became a Necessity, Not a Luxury
2024 Review: Consolidation to Address Identity Sprawl
The trend toward unified platforms dominated in 2024 as organizations faced the operational chaos of identity sprawl. Enterprises managing identities across siloed systems, from SaaS apps to legacy on-prem systems, struggled to maintain visibility and enforce consistent policies. According to a Gartner report, nearly 60% of enterprises prioritized consolidating their IAM tools to reduce complexity and improve efficiency.
2025 Outlook: Integration and Efficiency at Scale
Unified platforms will become the default approach for IAM. Enterprises will demand solutions that offer centralized management across all environments—on-premises, cloud, and SaaS. These platforms must also provide deep integrations with adjacent security tools such as SIEM and ITDR.
Actionable Takeaways
- Audit Your IAM Tools: Identify and eliminate redundancies to streamline operations.
- Invest in Integration-Ready Platforms: Look for IAM solutions that integrate with broader security tools, such as SOAR and endpoint detection.
- Centralize Visibility: Ensure you have a single pane of glass to manage and monitor all identities.
2. Zero Trust Moved from Strategy to Execution
2024 Review: From Buzzword to Practical Deployments
In 2024, zero trust evolved from a conceptual strategy to real-world implementations. Forrester highlighted the rise in zero-trust deployments as enterprises moved to secure hybrid workforces and sensitive data. However, implementation challenges—particularly around APIs and IoT devices—remained a common theme.
2025 Outlook: Expansion to All Identities
Zero-trust frameworks will continue to expand beyond human identities. Expect organizations to extend continuous validation principles to machine identities, ensuring APIs and IoT devices are governed as rigorously as employees.
Actionable Takeaways
- Start with Privileged Access: Apply zero-trust principles to privileged accounts and sensitive data first.
- Integrate Continuous Validation: Replace one-time authentication with ongoing monitoring of behavior and context.
- Focus on Non-Human Identities: Enforce zero-trust policies for APIs and IoT devices.
3. AI Transformed IAM from Reactive to Predictive
2024 Review: Real-Time Insights Revolutionized IAM
AI-powered IAM solutions gained traction in 2024, transforming identity management from reactive to proactive. Tools like Microsoft Entra and Ping Identity incorporated AI to detect anomalies and automate access reviews. According to a report from CSO Online, organizations using AI for identity management reduced insider threat response times by up to 30%.
2025 Outlook: Prediction and Policy Optimization
AI will evolve to offer predictive insights, enabling enterprises to identify potential identity-based risks before they materialize. It will also dynamically optimize policies, adjusting access controls based on real-time risk levels.
Actionable Takeaways
- Leverage AI for Anomaly Detection: Use AI to flag unusual access patterns in real-time.
- Adopt Predictive Capabilities: Choose solutions that anticipate risks rather than reacting to them.
- Automate Policy Adjustments: Allow AI-driven tools to recommend and implement changes to access controls based on behavior analytics.
4. Identity Threat Detection and Response (ITDR) Took Center Stage
2024 Review: Identity-Based Threats Dominated
Identity-based attacks surged in 2024, prompting the rise of ITDR as a critical capability. According to an article by Dark Reading, attackers increasingly targeted credentials, exploiting vulnerabilities in traditional detection tools. ITDR tools helped organizations detect compromised credentials, unusual privilege escalations, and insider threats in real time.
2025 Outlook: ITDR as a Standard Capability
In 2025, ITDR will be a core component of IAM platforms. Enterprises will expect ITDR to integrate seamlessly with broader security operations, offering actionable insights and automated responses to identity-based threats.
Actionable Takeaways
- Focus on Privileged Accounts: Use ITDR to monitor and protect high-value accounts with elevated permissions.
- Automate Incident Responses: Leverage ITDR tools that can revoke access or isolate compromised accounts instantly.
- Integrate with SIEM: Combine ITDR insights with broader threat detection systems for greater context.
5. Regulatory Pressure Drove Advances in Identity Governance
2024 Review: Compliance Became a Key IAM Driver
Regulatory pressure intensified in 2024, with enterprises facing stricter mandates under GDPR, HIPAA, and regional data protection laws. A report by Cybersecurity Dive found that 70% of enterprises adopted automated IAM tools to streamline access reviews and ensure audit readiness.
2025 Outlook: IAM as a Compliance Enabler
IAM platforms will go beyond meeting regulatory requirements to actively simplify compliance workflows. Real-time access reviews and automated reporting will help enterprises stay ahead of evolving regulations while reducing manual workloads.
Actionable Takeaways
- Automate Compliance Reporting: Use IAM tools that generate audit trails and flag non-compliance in real time.
- Streamline Access Reviews: Implement systems that automatically schedule and execute access reviews for sensitive systems.
- Map IAM to Compliance Goals: Align IAM practices with specific regulatory requirements to ensure smooth audits.
6. Third-Party and Supply Chain Access Became a Critical Focus
2024 Review: Supply Chain Risks Exposed
Third-party access remained a critical vulnerability in 2024, with high-profile breaches underscoring the need for better vendor identity governance. Research by The Hacker News showed that 62% of breaches involved third-party credentials, highlighting gaps in onboarding, monitoring, and offboarding processes.
2025 Outlook: Zero Trust for Third Parties
Enterprises will adopt stricter onboarding and offboarding workflows for external users. Zero trust principles, including adaptive authentication and continuous monitoring, will be applied consistently to third-party identities.
Actionable Takeaways
- Set Access Limits: Ensure third parties only have access to the systems and data necessary for their role.
- Implement Automated Workflows: Use IAM platforms to manage third-party lifecycle events, from onboarding to offboarding.
- Monitor Third-Party Behavior: Continuously monitor vendor access to detect and respond to suspicious activity.
7. IoT Identity Management Took a Front Seat
2024 Review: IoT Devices Increased Complexity
The proliferation of IoT devices in enterprise environments brought unique IAM challenges in 2024. A report by IoT World Today revealed that 45% of enterprises lacked visibility into IoT device identities, creating significant security gaps.
2025 Outlook: IoT Identities as First-Class Citizens
IAM solutions will treat IoT devices as equal to human identities, enabling real-time authentication, granular policy enforcement, and behavioral monitoring.
Actionable Takeaways
- Inventory IoT Devices: Maintain a real-time registry of all IoT devices and their associated identities.
- Apply Role-Based Policies: Enforce access controls tailored to the role and criticality of each device.
- Monitor Behavior: Use analytics to detect unusual activity from IoT devices, such as unauthorized data transmissions.
Preparing for 2025’s IAM Landscape
The trends of 2024 emphasized that IAM is no longer just a supporting function—it’s the foundation of enterprise security. By understanding and adapting to these trends, CISOs can future-proof their organizations against evolving threats while enabling operational efficiency and compliance.
At Linx Security, we’ve helped enterprises navigate the complexities of IAM, turning challenges into opportunities. As you prepare for 2025, let us guide your journey to a more secure and resilient IAM strategy.
Ready to align your IAM strategy with 2025’s trends?
Contact us for a consultation or explore Linx Security’s cutting-edge IAM solutions to future-proof your enterprise.
Visibility without action is like an expensive car without a motor—impressive but ultimately useless. In today’s rapidly evolving digital landscape, managing identity and access is one of the most critical challenges organizations face. With employees, contractors, and systems accessing a mix of SaaS platforms, on-premises infrastructure, and multi-cloud environments, ensuring that access is appropriate, compliant, and secure is no small feat. While many organizations excel at detecting risks like over-provisioned accounts or dormant entitlements, far fewer are equipped to address these vulnerabilities effectively and in real time.
This is where remediation takes center stage. Effective identity governance and security aren’t just about having policies in place or identifying risks—they hinge on the ability to take swift, decisive action. Without remediation, gaps between governance policies and security enforcement widen, exposing organizations to threats, inefficiencies, and compliance violations.
Why Real-Time Remediation is Vital
At the heart of identity governance lies the ability to ensure that access policies are consistently enforced across users, roles, and systems. Security, on the other hand, seeks to minimize risk by addressing vulnerabilities such as privilege sprawl or dormant accounts. These two disciplines—governance and security—must work in unison. Real-time remediation acts as the bridge, enabling organizations to move seamlessly from policy to action and from detection to resolution.
Governance and Security: A Unified Imperative
Governance frameworks such as ISO 27001, GDPR, NYDFS, and SOX require organizations to define and enforce strict access policies. Yet, without security mechanisms to ensure compliance, these frameworks remain aspirational. Security initiatives like least-privilege enforcement rely on governance to define appropriate access levels but require real-time remediation to maintain them dynamically.
A global retail company discovered during a compliance audit that 12% of employees retained access to inventory systems long after transitioning to non-operational roles. While governance frameworks mandated role-based access policies, the company’s manual processes delayed remediation, leaving these permissions active for months. By integrating Linx Security’s automated workflows, the organization ensured immediate adjustments to permissions during employee transitions, maintaining both compliance and security standards.
Real-Time Remediation in Action
1. Enforcing Least Privilege at Scale
Least-privilege access is a cornerstone of both governance and security, but maintaining it in dynamic, large-scale environments is a challenge. Without real-time remediation, privilege drift—where users accumulate excessive permissions over time—can undermine governance principles and expand the attack surface.
Financial institutions implement Linx Security to enforce least privilege dynamically. When a project-based contractor is granted elevated permissions to work on a trading system, Linx Security’s time-bound access controls automatically revoke these permissions upon project completion. This approach ensures compliance with the institution’s internal governance policies while minimizing risk exposure.
2. Automating the Joiner-Mover-Leaver (JML) Lifecycle
Managing access during the JML lifecycle is critical to ensuring governance and security. Onboarding (joiner), role transitions (mover), and offboarding (leaver) events are common sources of access mismanagement, leading to dormant accounts or lingering permissions.
Healthcare providers face challenges adhering to HIPAA regulations due to delays in deprovisioning accounts after employee departures. With Linx Security’s integration into HR and IT systems, offboarding triggers now initiate immediate access revocation for all associated systems, from electronic health records to billing platforms. Additionally, when employees move roles, their permissions are adjusted to align with their new responsibilities, preventing access overlap.
3. Continuous Monitoring and Policy Alignment
Identity governance isn’t static; it requires continuous monitoring and realignment of access with evolving policies and roles. Automated workflows for detecting and remediating anomalies ensure governance and security remain tightly coupled.
One of our SaaS company partners using Linx Security identified excessive permissions in its engineering department. Some developers had access to sensitive customer data that was not relevant to their roles. Linx’s platform flagged the misalignment and initiated an automated identity risk remediation workflow, revoking inappropriate access and maintaining an audit trail to support compliance efforts during external audits.
How Real-Time Remediation Enhances Security and Governance
Real-time remediation doesn’t just address immediate risks—it strengthens the foundation of an organization’s identity governance and security strategy. Here’s how:
- Dynamic Policy Enforcement: By aligning access with roles, functions, and organizational policies in real time, organizations ensure continuous compliance with governance frameworks.
- Minimized Attack Surface: Dormant accounts and privilege sprawl are proactively addressed, reducing the number of exploitable entry points for attackers.
- Audit-Ready Transparency: Automated workflows maintain detailed logs of every action, simplifying compliance with regulations like GDPR, HIPAA, and SOX.
- Risk-Based Prioritization: Linx Security enables organizations to focus remediation efforts on the most critical risks, such as administrative privilege escalations or unauthorized lateral movement.
A Holistic Approach to Governance and Security
The success of identity governance and security depends on their ability to work together seamlessly. Governance provides the blueprint, defining what access is appropriate, while security ensures these policies are enforced dynamically. Real-time remediation bridges the gap by transforming policies into action, reducing risk, and enabling continuous compliance.
At Linx Security, we specialize in unifying governance and security through proactive, automated remediation. Our platform empowers organizations to enforce policies, reduce vulnerabilities, and adapt to the complexities of modern identity governance and administration with confidence.
Conclusion: From Policy and Risk to Action
Identity governance and security are no longer optional in today’s hyper-connected enterprise environments—they are fundamental. But governance without action and security without policy alignment are incomplete. Real-time remediation is the critical element that unites these disciplines, allowing organizations to detect risks, take action, and maintain compliance in an ever-changing landscape.
If you’re ready to elevate your identity governance and security strategy, Linx Security is here to help. Together, we can close the governance-security gap and build a more secure future.
Offboarding employees has always been a crucial process in maintaining a secure environment, but as organizations grow, the complexity of managing user access increases significantly. One of the biggest yet often overlooked vulnerabilities occurs when users are only partially offboarded. This scenario happens when employees leave the company, but some of their access to cloud applications, internal tools, or shared resources remains intact.
The risks posed by this oversight are numerous, spanning both security and governance:
Security Risks
- Unauthorized Access: Partially offboarded users may retain access to sensitive data or systems, either unintentionally or through deliberate misuse. If their credentials remain active, these former employees can still access critical applications like email, file storage, or CRM systems.
- Insider Threats: In some cases, employees who have left on negative terms could use their still-active accounts to leak data or disrupt operations. Even in cases where the departure was amicable, having unmonitored, lingering access opens doors to potential misuse.
- Compromised Credentials: Former employees may become an easy target for attackers. If a hacker compromises their inactive but still valid credentials, they gain entry to the organization's systems undetected, as the user may no longer be closely monitored.
- Audit and Compliance Failures: Regulatory frameworks like GDPR, HIPAA, and PCI DSS require organizations to demonstrate control over user access to sensitive data. Partially offboarded users represent a significant non-compliance issue that can lead to audits, fines, or legal penalties.
Governance Risks
- Lack of Visibility: When offboarding isn't fully automated or governed by a centralized identity management solution, it becomes difficult for IT or security teams to have a clear view of which users still retain access to which systems. Shadow IT often arises, leaving unmanaged access risks.
- Policy Enforcement Failures: Identity governance frameworks require a consistent application of policies across user identities. In the case of partially offboarded users, those policies are often bypassed due to poor oversight, leading to a lack of proper controls around access and data security.
- SaaS Sprawl: Cloud environments are highly dynamic, and as more SaaS applications are introduced, the chances of users retaining access to unmonitored resources increase. Without clear governance, users with orphaned accounts across applications represent a significant security gap.
How Linx Security Solves This Problem
At Linx Security, we understand the challenge of managing user access throughout an employee’s lifecycle, especially when it comes to the offboarding process. Here’s how we help organizations mitigate the risks associated with partially offboarded users:
- Comprehensive Identity Lifecycle Management: Linx Security ensures that user identities are centrally managed from onboarding to offboarding. Our solution automates deprovisioning processes across all integrated applications, ensuring that no lingering access is left behind.
- Real-Time Access Visibility: We provide security teams with real-time dashboards that offer complete visibility into every user’s access across cloud applications, infrastructure, and shared resources. This allows for immediate detection and remediation of orphaned accounts or partially deprovisioned users.
- Automated Policy Enforcement: With Linx Security, organizations can enforce access policies consistently across their entire ecosystem, ensuring that when an employee leaves, all their permissions and credentials are immediately revoked. This aligns with governance and compliance requirements to prevent unauthorized access.
- Risk-Based Access Reviews: To further strengthen governance, Linx Security enables periodic, risk-based access reviews. This ensures that even accounts that might have been missed during the initial offboarding are caught and deactivated before they become a threat.
- Audit-Ready Compliance Reporting: Our platform generates audit-ready reports that demonstrate your organization’s ability to control and govern user access, helping you stay compliant with industry standards and regulations like PCI DSS, SOX, and HIPAA.
Conclusion
Partially offboarded users present a serious threat to security and governance, but with the right tools in place, organizations can effectively mitigate these risks. Linx Security’s comprehensive identity and access management solution ensures that no user is left with unintended access to sensitive systems and data. By automating offboarding and enforcing strict governance, we help you protect your organization from the hidden dangers of incomplete de-provisioning.
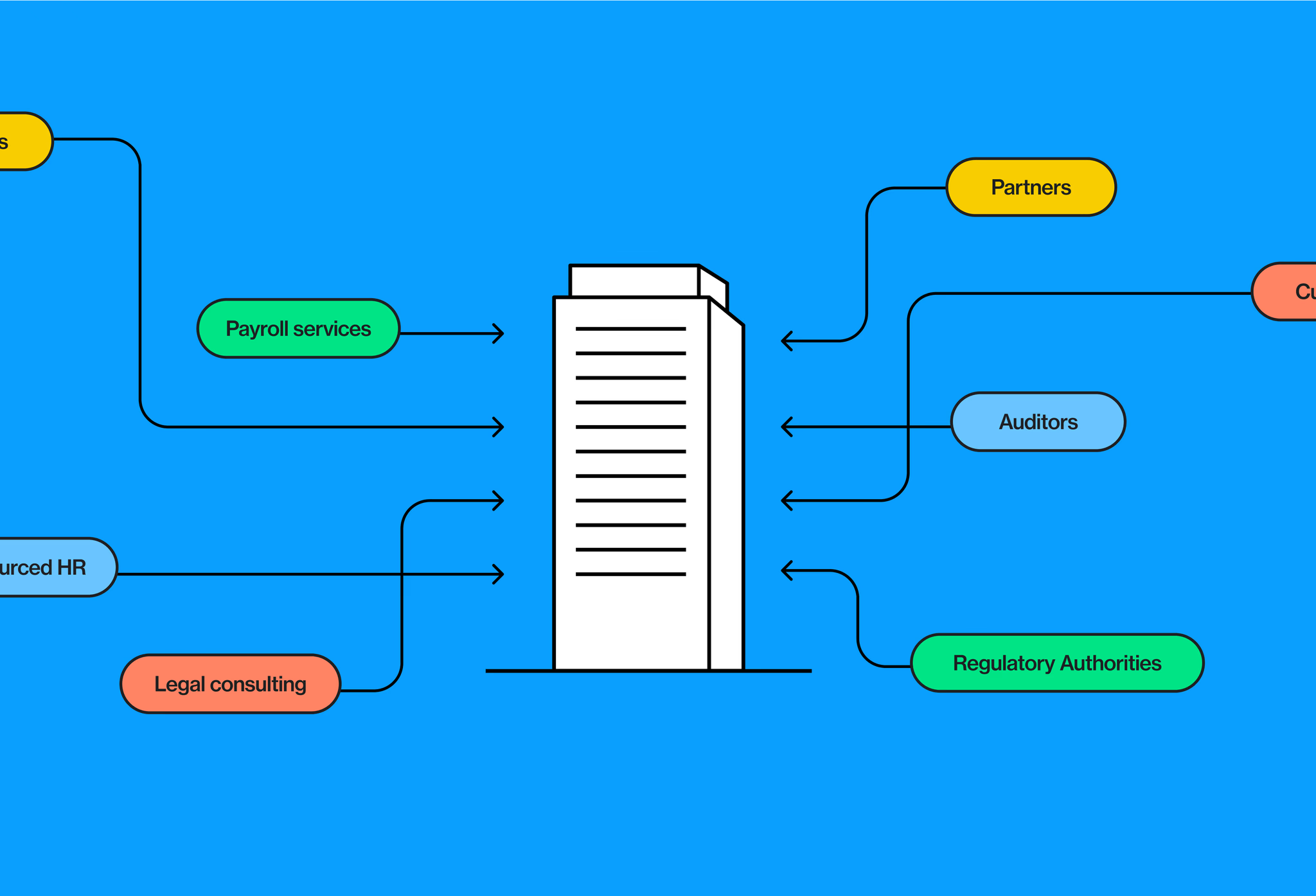
What Makes Access for Non-employees So Challenging, and How Can You Solve It?
In today’s evolving business landscape, companies are increasingly reliant on a workforce that extends beyond traditional, full-time employees. Temporary workers, contractors, partners, and even vendors now play critical roles within organizations. This trend towards a hybrid workforce brings additional flexibility but also challenges, particularly in managing and governing the access of these non-employees. According to Gartner, 45% of security breaches involve non-employee users, underscoring the need for greater visibility and oversight in managing their access.
What makes access for non-employees so challenging?
- Complex and diverse access needs - Unlike employees, non-employees often have unique and variable access needs. Contractors may require temporary access to specific systems, while vendors may need ongoing access to certain resources, albeit with fluctuating levels of permission. Governing this diverse set of access requirements can be complex, especially when access requests frequently change over time.
- Limited visibility and oversight - Non-employees often exist outside of standard HR processes and systems, making it difficult to track their access lifecycle—onboarding, access management, and offboarding. Limited visibility into who has access to what increases the risk of unauthorized access, especially if permissions aren’t terminated promptly.
- Increased security risks - Since non-employees are often not fully integrated into the organization’s culture or familiar with its security practices, they could inadvertently compromise sensitive information and neglect the security processes implmented in the organization. According to Forrester, 63% of breaches are due to compromised access credentials, including those of contractors and other third-party users.
- Regulatory compliance challenges - Governing non-employee access is crucial not only for maintaining security but also for meeting regulatory requirements. Regulations like GDPR, HIPAA, and SOX mandate stringent controls over access to sensitive data. Without a structured process for managing non-employee access, organizations risk failing audits and incurring fines.
- Operational inefficiencies - Manual access management processes can be time-consuming and error-prone. For organizations that rely heavily on non-employees, the administrative burden can become overwhelming, leading to delays in granting necessary access or, worse, lingering access for users who no longer need it. According to the Identity Management Institute, 51% of organizations experience operational inefficiencies due to fragmented and manual access management processes for non-employees, further stressing the need for identity governance automation.
The key to solving for non-employee access
To effectively govern non-employee access, organizations need a modern approach that goes beyond traditional access management capabilities and provides the following essential capabilities:
- Discovery and management for non-employees - It’s crucial to keep non-employee accounts accurate and up-to-date. Without regular oversight, entitlement creep or orphaned accounts can occur—non-employees may accumulate unnecessary access over time, or accounts may remain active even after a contract ends. Having your solution serve as a dedicated repository for non-employee identities allows easy input and monitoring of relevant details while enforcing the necessary controls for close management.
- Follow the principle of least privilege - No employee or non-employee should have more access than needed to get their job done. This is best achieved through role-based access, which provides permissions based on roles instead of individual entitlements. Roles can easily be applied to well-managed non-employees as well as employees.
- Comprehensive identity lifecycle management - Manual provisioning can be labor intensive and take weeks before new employees have the access they need. This can lead to a frustrating experience for both the employee and non-employee and will cost the organization time and money. However, sloppy onboarding for the sake of speed can lead to security risks. While off boarding does not seem as time sensitive since no one is waiting on access, it is even more important from a security perspective.
Your solution should facilitate end-to-end access lifecycle management for non-employees, including automated onboarding, real-time access provisioning and de-provisioning, and tracking access over time. By automating these processes, organizations can ensure that access is consistently managed and immediately terminated when it is no longer needed. - Automated access reviews and certifications - Periodic access reviews and certifications are critical for ensuring that non-employees only have access to the resources they need. Your solution should provide automated access review workflows that facilitate timely review and re-certification processes. This reduces the administrative burden on IT teams while ensuring compliance with security policies.
Conclusion
Effectively governing non-employee access requires a modern solution. As the workforce continues to evolve, organizations must prioritize non-employee access governance to maintain security, meet compliance requirements, and reduce operational inefficiencies. By investing in a solution that meets these needs, organizations can not only manage non-employee access effectively but also enable a more agile, secure, and compliant digital environment.
Ready to manage non-employee access?
Contact us today to learn how we can help.
Sign up to get new articles & updates from the Linx team sent straight to you.