Linx Blog
How Forrester defines the new workforce identity stack
Forrester defines workforce identity security platforms as unified platforms that govern, administer, and enforce identity security safeguards across workforce users, human and nonhuman, to protect networks, applications, and data. These platforms pull together identity data sources, SSO, MFA, access management, and identity governance, then layer on AI-driven identity intelligence and analytics.
In other words, this is no longer “just IAM.” The platform is expected to:
- Deliver identity-centric security and help prevent identity-based attacks by eliminating security gaps and reducing the attack surface.
- Maintain regulatory compliance and audit readiness across frameworks like SOX, GDPR, PCI DSS, and DORA.
- Improve workforce productivity with streamlined onboarding, access requests, SSO, and self-service.
Forrester also calls out the growing pressure from nonhuman identities and AI:
- The proliferation of nonhuman identities (NHIs) like service accounts, workloads, APIs, and AI agents is now a primary challenge that drives identity sprawl and business risk.
- The agentic AI workforce is named as the top disruptor, requiring new governance, lifecycle, and risk detection models, along with support for emerging AI security protocols and standards.
This is exactly the world Linx was built for: a mix of humans, machines, and AI agents that all need access, all the time.
Where Linx shows up in the Forrester Landscape
The report covers 32 vendors globally. Linx Security is listed among those vendors, alongside hyperscalers, long-time IAM players, and a small number of specialized identity security platforms.
Forrester then breaks the market into:
- Core use cases: identity and access policy administration, workforce onboarding and offboarding, secure workforce access, and regulatory compliance reporting.
- Extended use cases: IAM process automation, identity governance, identity security posture management, identity threat detection and response, machine and AI agent identity management, and third-party access management.
In the extended use case matrix, Linx is listed in three specific areas:
- Identity governance
- Machine and AI agent identity management
- Identity security posture management
Those three are not generic checkboxes for us. They are the center of how the Linx platform is designed.
Why these areas matter, and how they map to what Linx does
1. Identity governance: modern IGA that people actually use
Forrester treats identity governance as one of the extended use cases that differentiates workforce identity platforms beyond basic IAM.
In practice, that means:
- Running access reviews that do more than produce spreadsheets.
- Enforcing least privilege without creating months of manual role modeling.
- Proving to auditors, at any time, who has access to what and why.
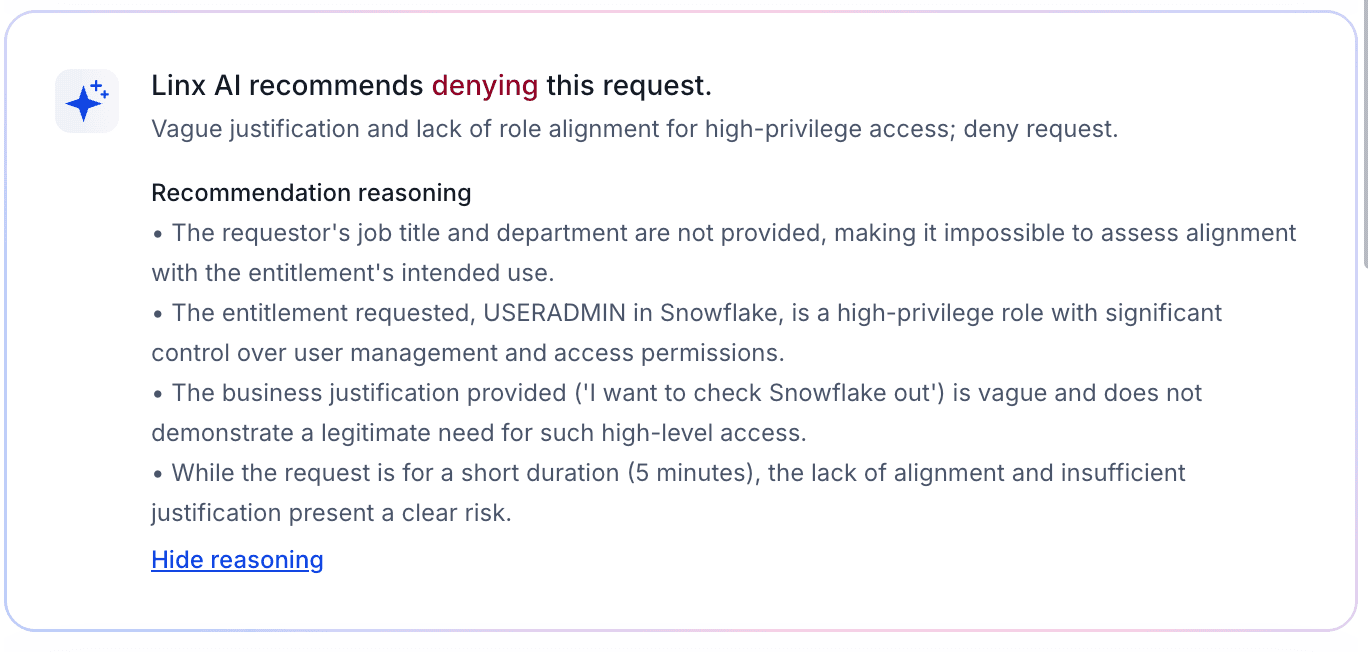
Linx leans into modern IGA with AI-assisted access reviews, contextual recommendations, and immutable, auditor-ready reports. The goal is simple: get your certifications done faster, with higher quality decisions, and leave behind an evidence trail that stands up in front of a regulator or a board.
2. Machine and AI agent identity management: securing the agentic workforce
Forrester calls out the proliferation of nonhuman identities and the rise of agentic AI as both a primary challenge and the top disruptor in this market.
This is where Linx has been investing heavily:
- Treating AI agents, service accounts, and workloads as first-class identities, not an afterthought.
- Giving security teams visibility into what those agents can reach, and what they actually use.
- Applying the same least-privilege, lifecycle, and review controls to nonhuman identities that you already expect for human users.
As enterprises push more work into autonomous agents, this becomes a board-level risk question, not a tooling detail. Seeing Linx recognized in this emerging use case is a strong signal that we are aligned with how the category will evolve over the next few years.
3. Identity security posture management: from “who has access” to “what should we fix first”
Forrester describes how workforce identity platforms are increasingly defined by AI-driven identity security intelligence. They are expected to detect drift and misconfiguration, and support real-time identity threat detection and response.
That is essentially the identity security posture management problem:
- You need a complete map of identities, entitlements, and relationships.
- You need to know which patterns represent real risk, not just noise.
- You need a path to remediate excessive or toxic access, not just report on it.
Linx tackles this with graph-based visibility across SaaS, cloud, and business apps, layered with AI that flags excessive privileges and risky access paths. Then, instead of stopping at “observability,” we allow teams to actually remediate from within the platform, with automation where appropriate and human review where needed.
What this means for customers
This Forrester Landscape is not a ranking or a Wave. It is a map of who is in the game and how the market is shifting. Being included is step one. Being listed in extended use cases that sit at the heart of the next identity decade is the more important part.
For our customers and partners, the message is straightforward:
- You are not alone in feeling that traditional IAM and legacy IGA were not designed for today’s mix of humans, machines, and AI agents.
- Analysts now describe the market in terms that match the problems you are bringing to us every week: posture management, governance that works at scale, and control over nonhuman identities.
- Linx is recognized as one of the vendors focused on exactly those problems, not as a generalist tool trying to be everything to everyone.
We will keep sharing more detail on how we approach identity governance, posture, and AI agent control over the coming months. For now, this report is a useful validation that the hard problems you are asking us to solve are the same ones reshaping the entire workforce identity security market.
Find the full report here: Forrester Workforce Identity Security Platforms Landscape.
Most organizations still deal with a lot of standing access. A user gets elevated access and we forget to revoke it, or someone switches roles and keeps their access from the old one. Our attack surface grows with each standing permission. Just-in-time access flips that default. You grant only what is needed, exactly when it is needed, and you remove it as soon as the work ends.
In this article I hope to give identity and security teams a practical path to make JIT access the standard operating model. We define JIT, show how it fits with RBAC and ABAC, explain where it works best, explore how agents change the picture, and outline how to build, roll out, and measure a program that improves both productivity and security.
What is JIT (Just-In-Time)?
Just-in-time access issues time-bound and scope-bound permissions on demand, then revokes them automatically. Think of it as least privilege with a clock and a clear scope. Unlike a standard access request, expiry is part of the grant. No one needs to remember to remove anything later.
JIT began as an emergency scenario, like when an admin needs elevated access quickly to resolve an urgent issue. Modern identity platforms and cloud controls now support it across a much wider set of tasks. JIT can be the default for any permission you do not use daily, including sensitive SaaS roles, database privileges, cloud consoles, CI pipelines, and internal admin functions.
How JIT Works With RBAC and ABAC
Role Based Access Control assigns access based on membership in a role. You define a role once and map it to entitlements. For example, everyone with the Marketing role gets HubSpot and Canva.
Attribute Based Access Control grants access when a policy evaluates to true across attributes of the user, resource, action, and environment. The policy defines who qualifies, not a static group. For example, grant HubSpot and Canva to users whose role is Marketing, employment type is FTE, location is US, and manager is John Smith.
Just in time adds duration and task. Keep the baseline role small. Use ABAC to narrow eligibility and conditions. When a task requires elevation, issue a short-lived entitlement tied to a specific action and resource. ABAC decides who qualifies under current conditions, and JIT limits how long and how broadly the grant applies. You can also use ABAC to block requests outright if the requester does not meet basic requirements like MFA or compliant device.
When is it Time for Just-In-Time?
JIT fits two patterns. The first is routine elevation on a predictable cadence. Consider quarter-close finance tasks, maintenance windows, or periodic schema changes. The second is ad hoc work where someone needs temporary rights to unblock an incident or enable a deployment.
Ownership matters in both cases. Requestors should not need to be security experts. Application and entitlement owners define what can be JIT-granted, under which conditions, and for how long. Security teams codify guardrails and step in for high-risk changes or separation of duties checks. Approvals start with the owner who understands the operation, with security engaged when risk or policy requires it.
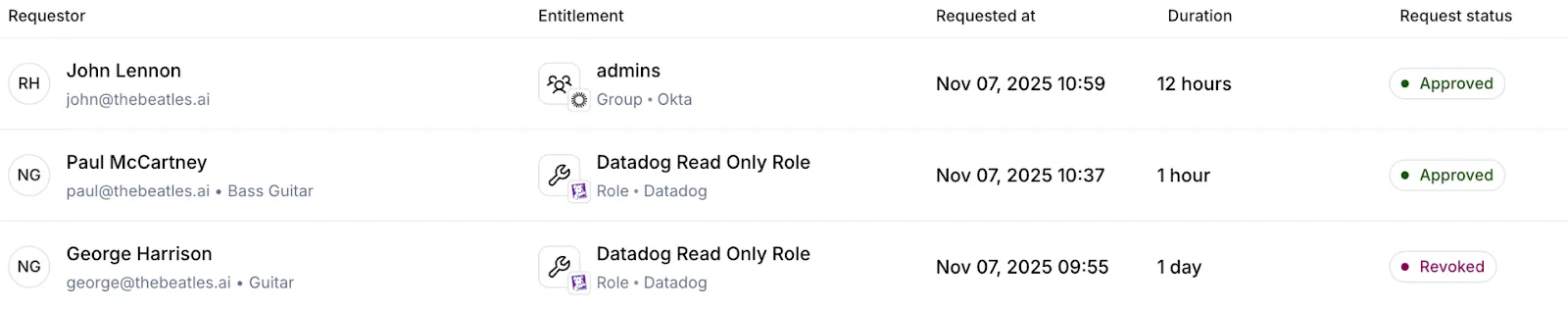
A simple example illustrates the idea. A product manager occasionally needs admin rights in a support tool to add a contractor. Today that person might keep admin forever because it is convenient. With JIT, they request a task-scoped admin profile that expires in X minutes. The system records who, what, why, and for how long access was granted. The job gets done, and the background risk stays low.
Agents And Non-Human Identities
AI agents are now autonomous actors inside the enterprise. They make decisions, access systems, and execute tasks with little human oversight. That makes them identities in their own right, not just wrappers around service accounts or API keys. Treat them as first-class identities with owners, clear purposes, and explicit scopes.
Most teams cannot answer three basic questions today. Which agents are running in our environment. What systems can they access? What permissions do they actually hold? This visibility gap is the core risk as adoption accelerates.
Agents behave differently from traditional NHIs. A service account follows fixed logic. An agent interprets context, adapts, and tries alternate paths until it completes the task. It operates at high speed and at scale. If it inherits broad standing rights, the blast radius grows quickly.
The model that works looks a lot like how you govern people, with tighter controls and shorter windows. Start with an agent registry. Record owner, purpose, allowed tasks, baseline scopes, and last activity. Link each agent to the machine credentials it may use and to the data it can touch. Represent these relationships in your identity graph so every request is evaluated in context.
Just-in-time access is essential for agents. Give the agent only the permission it needs for the specific task and for a short period. Do not let it reuse a human sponsor’s standing rights. When the timer expires, revoke tokens, sessions, and keys.
Round out the guardrails with a small set of practices that scale:
- Identity profiles that define purpose, baseline permissions, and ownership
- Human-in-the-loop approval for any elevation beyond the baseline
- Continuous monitoring for unused rights, anomalous behavior, or scope creep
- Automated identity risk remediation that revokes excess, suspends risky agents, and notifies owners
This approach keeps autonomy without losing control. You gain clear accountability, smaller blast radius, and audit-ready records for every decision. Most important, you align agent productivity with least privilege by default, not as an afterthought.
A JIT Architecture That Scales
JIT thrives when four layers work together and feed one another.
1) Visibility
Start with an accurate catalog of identities, entitlements, applications, resources, and owners. Include people, service accounts, workload identities, and agents. Map who can grant what. Assign ownership for every entitlement and admin function. Integrate data from your IGA, directories, cloud accounts, SaaS admins, and data platforms. Without this map you cannot know what you are granting or who should approve it.
2) Policy And Decision
Define who can request what, under which conditions, and for how long. Use ABAC to enforce basic security requirements. Link higher risk actions to change records. Tier approvals by risk (what gets auto-approved vs. what needs human review).

3) Intelligence
Add context to each request. Does the request align with the requester's job title and team? Do other team members have this access? Does the user have a history of violations? Present recommendations that reduce cognitive load for approvers. The goal is not to replace judgment. It is to give the resource owner structured context so they can decide quickly and confidently.
4) Fulfillment And Audit
Provision at the smallest practical unit. Prefer ephemeral roles, short-lived tokens, and session policies rather than group adds. Revoke everything when the timer expires, including sessions and keys. Write a durable audit trail that captures requestor, approver, reason, scope, and duration. Index every grant so user access reviews become faster and more meaningful.
Rolling Out JIT
Start where the impact is highest. Choose a sensitive SaaS app and a production cloud account. Inventory admin actions, define owners, and mark which actions are JIT-eligible. Set short default durations and clear approval paths. Run a small pilot with people who understand the tasks and can provide actionable feedback.
Limit the audience at first. You can hide the JIT entry point from general users until owners and security are comfortable with the flow. As confidence grows, expand who can request JIT and add more actions and teams.
Make audit an explicit outcome. Every JIT grant should produce an easy to read record for compliance. This reduces manual effort during periodic reviews and gives auditors clear evidence of least privilege.
Guardrails For Agents
Agents need the same rigor as people, plus a few extras. Maintain a registry of agents with owner, purpose, allowed tasks, and data sensitivity. Use short-lived credentials with narrow scope. Avoid reusable keys and prefer brokered, time-bound tokens. Require human initiation for scope changes. Agents may request within their allow list but cannot extend it on their own. Build a kill switch that revokes all agent tokens at once. Connect it to anomaly detection so you can respond quickly without guesswork.
Measuring JIT Success
A focused set of metrics shows progress. Track the percent reduction in standing high-risk entitlements. Measure mean time to elevation and approval success rate. Watch median JIT session length and the share that end by auto revoke. Monitor reviewer load during access reviews and incidents linked to stale permissions.
The target state is clear. Elevation for legitimate work is fast. Background risk trends down. If both lines move in the right direction, your model is working.
Common Failure Modes And Fixes
Approval fatigue is the most common failure. Owners and security get overwhelmed by noisy requests. Reduce volume with clear task packs and strong defaults. Use recommendations so owners see a simple approve or deny with the right context.
Temporary group adds are another trap. Groups linger and create blind spots. Prefer ephemeral roles or policy attachments that expire automatically. When groups are unavoidable, require an expiry and verify revocation after the window closes.
Agent inheritance is a quiet risk. Do not let agents reuse human standing rights. Bind them to their own service principals and JIT policies.
How Linx Implements JIT
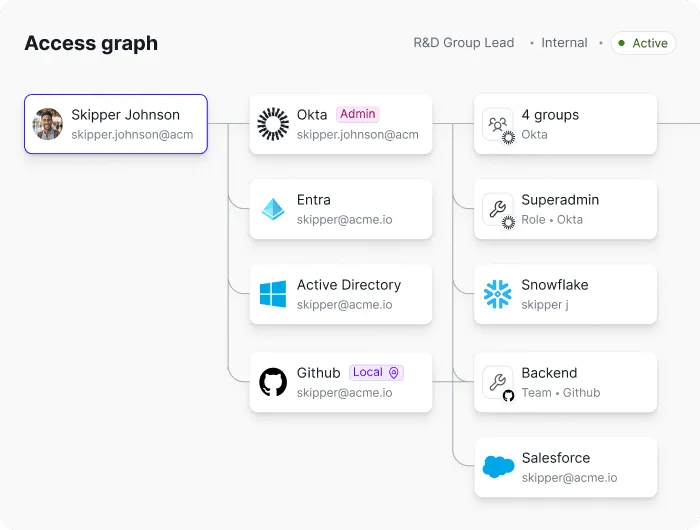
Linx treats identity as a security problem first. The platform builds a graph that unifies people, non-human identities, and agents across SaaS and cloud. Every request consults this graph in real time. Risk signals and peer comparisons help owners decide quickly. Policies blend RBAC, ABAC, task context, and separation of duties.
Provisioning is granular. The system attaches the smallest scope required for the task, issues short-lived credentials, and tears them down on expiry. The same flow works for human users, workload identities, and agents. Approvals start with the resource owner and escalate by risk, which keeps security focused on the reviews that matter most. Every action writes a complete audit trail so access reviews and certifications become faster and more accurate.
Customers tell us the difference is the security-first lens. The goal is not only faster approvals or cleaner audits. The goal is safe productivity. JIT captures that goal by cutting background risk while keeping teams moving.
Bringing It Together
Standing access is quiet exposure that grows over time. Just-in-time and just-enough access, paired with dynamic access profiles is how you ensure that exposure stays at a minimum. You grant only what is needed, when it is needed, and you remove it on time.
Most identity teams have done the responsible work. You set up an IdP for SSO, enforced MFA, rolled out IGA, and protected admin paths with PAM. Yet privilege-creep lingers, offboarding is inconsistent in the details, and blind spots show up across SaaS, cloud, on-premise, and internal systems. That outcome is not a bad strategy or a failure to follow best practices. It is the natural result of growth and complexity. People move roles, apps multiply, automation creates new access edges, and non-human identities are on the rise. Meeting that reality calls for a new way to understand and act on identity.
That is the point of an Identity Visibility and Intelligence Platform (IVIP). An IVIP is a single place that unifies identity data, models how permissions actually relate to resources, and presents decisions you can carry out in the flow of work. It does not discard what you already have. It helps you run it better. In some organizations it also starts to absorb work that once lived in a legacy IGA suite. The goal is simple - make identity management easier and safer for admins, security teams, and end users.
The challenge with today’s stack
Identity programs grew up in a world of clearly bounded systems. Today the edges are fuzzier. A single user can participate in or hold a mix of IdP groups, application roles, inherited permissions, and temporary tokens. A single workload can carry keys and service principals that unlock powerful APIs. None of these are bad on their own. The problem is that the important questions are relational. Who can do what on which resource. What breaks if we remove this group? Which rights are unused and could be reduced?
Tabular inventories struggle with relational questions. They are good at counting, not at explaining. When decisions depend on how objects connect, you need a model that treats connections as first class citizens. That’s the gap I see IVIP stepping into.
Model relationships, not rows
Identity is a network of relationships. Human to account. Account to group. Group to role. Role to permission. Permission to resource. Owner to business unit. A platform that understands these links can answer the questions that matter and can do it in near real time. That is why a graph model is the right foundation. It makes it cheap to ask hard questions and safe to automate the obvious ones.
Here is a scenario that plays out every week: A senior engineer moves into a product role. HR updates the employee record. Some IdP groups change. On the surface, access looks correct. Yet a handful of admin privileges remain through inherited groups and application-local roles. The person no longer needs elevation but still holds write or admin rights in systems that touch production. A graph reveals the full path that keeps those rights alive. An IVIP should tie the HR event to identity edges, highlight the drift, show the exact inheritance that matters, and propose a safe remediation plan. You remove the unneeded entitlements, convert any remaining elevation to just-in-time, and keep the evidence for audit. No spreadsheets. No guesswork. No surprises six months later.
Intelligence that gets work done
Dashboards summarize. Intelligence drives change. Useful identity intelligence has three traits. It is explainable, precise, and actionable.
Explainable means you can see the path that produced the score or the alert. Breadth of access matters, but so do signals like inactivity, weak factors, external ownership, or exposure to sensitive resources. If you can explain and understand the calculation, you can defend the decision.
Precise means the recommendation is specific. Remove entitlement A and group B. Usage has been zero for 90 days. Peers in the new role do not hold either. Residual rights still allow task C. That is a decision a manager or owner can approve quickly.
Actionable means you close the loop in the same place you saw the issue. Revoke or reduce with one action. Time-bound a role and move on. Route a minimal approval to the true owner with context attached. The cost of doing the right thing needs to be low.
Coverage that matches how people and systems actually work
Coverage is not a list of connectors. It is a promise that the model reflects reality. That means human and non-human identities with clear ownership. SaaS, cloud, and on-prem applications with resource-level permissions, not just role names. Accounts inside and outside SSO, including application-local identities that bypass centralized controls. Peer and behavioral context so least privilege can be achieved with confidence. Segregation of duties checks that cross systems rather than living inside a single suite.
If one of these dimensions is missing, you introduce governance gaps or create an audit headache. An IVIP should bring them together so you can reason across them without stitching exports by hand.
What impact should an IVIP have?
Teams that adopt an IVIP, or a set of features that amount to the IVIP promise, should feel the impact in their first quarter. The first change is clarity. Dormant accounts, unused admin roles, overprivileged accounts, and other risks surface with owners attached and suggested fixes ready to go. The second change is decision quality. Right-sizing stops being personal and becomes a repeatable pattern. The platform shows the path, explains the risk, and proposes the minimal safe change. Approvals get shorter because the context is built in. The third change is operational momentum. Mean time to remediate identity risk becomes a real metric. Access becomes both safer and faster because defaults are designed to unblock work without widening blast radius.
There is also a cultural effect. Security and IT work from a single source of truth. Less time is spent reconciling spreadsheets. More time is spent making clear reductions that everyone understands.
A pragmatic way to start
Start by unifying what you already own. Ingest IdP, HRIS, IGA, PAM, the major SaaS applications, cloud providers, and the internal systems that carry the most risk. Normalize identities and connect both human and non-human principals to owners and resources. Then turn on opinionated detections. Focus on partially offboarded users, inherited admin rights, application-local accounts, orphaned service identities, risky factors, unused entitlements, and cross-system SoD. Require each finding to ship with owner, impact, and a proposed remediation.
From there, move to continuous right-sizing. Use usage data and peer baselines to convert standing privilege into least privilege. Prefer time-bound or approval-bound elevation over permanent admin. Simple policies go a long way. For example, remove any entitlement unused for a set number of days unless the owner opts out with a reason.
Close the loop with one-click actions and lightweight approvals. Record evidence automatically. Measure what matters: privileged account count, accounts outside SSO, time to remove unused admin access, percentage of time-bound elevation, and the number of automated right-sizing actions. These measures tie identity work to risk reduction and business velocity.
Use AI as an accelerator with guardrails. Summarize context, propose candidate roles, and prioritize onboarding. Keep data scoped to the task, respect privacy, and admit uncertainty rather than guessing. AI should help you move faster on correct work, not cover up missing data.
Where this leaves IGA
IGA remains useful for identity lifecycle management, certifications, and policy. IVIP complements that mission by providing full-fidelity visibility, trustworthy analytics, and closed-loop execution. In some environments IVIP will take over most decisioning and remediation while IGA handles specific compliance workflows. In others, teams choose to consolidate further. The point is not to keep every tool. The point is to meet today’s complexity with a model and workflow that can keep up.
The bottom line
You do not need to master every application’s permission model. You need a platform that understands them, unifies them, and gives you the fastest safe decision for each situation. That requires a relationship-aware model, explainable analytics, disciplined use of AI, and an operational loop that ends in a real change. Build IVIP on those principles and you will find issues sooner, fix them faster, and keep people moving without widening risk. That is what good identity looks like at modern scale.

Linx Is a Proud Participant in the Microsoft Security Store Partner Ecosystem
[New York, New York], USA — [09/30/2025] — Linx today announced its inclusion in the Microsoft Security Store Partner Ecosystem. Linx was selected based on their proven experience with Microsoft Security technologies, willingness to explore and provide feedback on cutting edge functionality, and close relationship with Microsoft.
"Microsoft is a foundational company in the identity space, and are uniquely aware of the importance of making modern identity security and governance accessible and easy to use. We’re honored to work closely with their security teams bringing that vision to life.”
Israel Duanis, CEO & Co-Founder, Linx
“The Microsoft Security Store is designed to simplify and strengthen how organizations approach cybersecurity. By offering a curated selection of trusted solutions and AI agents, we help Security and IT teams quickly find, purchase, and deploy technologies that integrate seamlessly with Microsoft Security. With simplified billing, streamlined deployment, and verified integrations, the Security Store empowers defenders to accelerate their response, improve their security posture, and focus on what matters most.”
Dorothy Li, Corporate Vice President, Security Copilot, Ecosystem and Marketplace
Linx is collaborating with Microsoft to help shape the development of the Microsoft Security Store, providing feedback on new features, integration experiences, and customer needs. By publishing certified solutions and AI agents that integrate seamlessly with Microsoft Security products, Linx is making it easier for organizations to discover, purchase, and deploy trusted security technologies. Through the Security Store, Linx is helping customers accelerate their security outcomes and simplify operations with solutions that are vetted, easy to deploy, and designed to work together.
The Microsoft Security Store is setting a new benchmark for cybersecurity procurement and deployment. By centralizing a wide range of security solutions and AI agents—organizations can now streamline how they discover, acquire, and operationalize advanced security technologies. With features like industry framework alignment, simplified billing, and guided deployment, the Security Store helps security teams reduce complexity, accelerate adoption, and maximize the value of their security investment
About Linx:
Linx gives identity teams unified visibility, governance, and risk remediation across human and non-human identities, for cloud, SaaS, on-prem, and custom applications. With a graph-powered view and AI guidance, Linx users enforce least privilege, replace standing access with JIT, and turn UARs from rubber-stamping into evidence-backed decisions.
Announcing the Linx AI-Agent: Autonomous Identity Security and Governance in Action
At Linx Security, our mission has always been clear: to make identity security and governance radically intelligent and radically autonomous. We started this journey by introducing the Linx AI-assistant, a natural language interface that made querying complex identity data effortless for every user. Then we launched the Linx MCP Server, which gave AI agents the ability to not just observe identity environments but to reason, act, and remediate at scale.
Today, we’re taking the next step forward: the Linx AI-Agent.
The Identity Challenge: Where Human Bandwidth Meets Its Limit
Identity teams today face a daunting paradox.
- Exploding complexity in systems and permission models. From SaaS apps with proprietary entitlements, to cloud platforms with layered IAM policies, to legacy systems with rigid roles - modern environments are a maze of overlapping permission models. Stitching these together into a coherent governance strategy is nearly impossible with human effort alone.
- Dynamic environments, static controls. Roles change, teams reorganize, apps are added, and policies lag behind.
- Too much access, not enough control. Employees often accumulate privileges they no longer need, creating hidden risk.
- Endless reviews and approvals. Security teams and managers spend hours rubber-stamping access requests and certifications, yet still worry about overlooking risk.
The result? A system designed to protect the enterprise becomes a bottleneck - slowing down the business, draining team resources, and leaving cracks attackers can exploit.
Traditional tools have focused on visibility or automation, but both fall short. Visibility tells you what is wrong, automation executes what you tell it to do - but neither can reason, adapt, or keep up with today’s dynamic environments.
That’s why we built the Linx AI-Agent: a trusted teammate that understands context, learns from patterns, and takes on the heavy lifting of identity governance.
The Real Business Impact of an Intelligent Identity Platform
The Linx AI-Agent isn’t just a smarter tool; it’s a shift in how identity governance and security gets done. From detecting risks, making governance decisions, executing remediation, and continuously optimizing policies, Linx AI-agent is there for you.
1. Risk Visibility Without Blind Spots
Proactively close identity gaps before attackers exploit them, without overwhelming teams with false positives, with AI-powered investigation.
Effortlessly perform complex queries by simply asking the questions interested in, and letting the Linx AI agent do the rest for you.
2. Access Approvals Without Guesswork
Faster approvals, fewer delays, and assurance that risk is never overlooked with AI-powered recommendations for access requests.
When an urgent JIT request comes in, the AI-Agent evaluates the context—who’s asking, what they need, when, and why—and guides approvers with confidence.
3. Compliance Without Rubber-Stamping
Compliance at scale, reduced audit fatigue, and confidence that reviews are meaningful - not just checkboxes with AI-powered recommendations for User Access Reviews (UARs).
During audits or quarterly certifications, instead of manually combing through spreadsheets, managers receive clear, contextual recommendations on which access to keep, remove, or further review.
4. Remediation Without Delay
Quickly reduce risks instead of chasing open remediation tickets that are pending busy IT teams. When risky or unused access is detected, the AI-Agent doesn’t just flag the issue -it provides clear remediation options and, where authorized, executes them automatically.
5. Onboarding Without Roadblocks
Faster employee productivity, reduced ticket volume, and stronger security baselines with AI-powered Access Profiles.
Imagine a new employee starting on day one. Instead of waiting weeks for the right permissions - or worse, copying access from a colleague—the AI-Agent builds a contextualized, least-privilege access profile instantly.
6. Agility Without Excess
Empower teams to move quickly without exposing sensitive systems to standing privileges with AI-powered Just-in-Time (JIT) Access Policies.
When a user needs elevated permissions for a critical system, the AI-Agent automatically reviews and analyzes the request, and provisions access for just the right duration - no more, no less.
7. Reporting Without Bottlenecks
Real-time visibility for executives, faster audit readiness, and less dependence on IT or data engineering with AI-powered Custom Reports.
Security leaders and auditors can request any report in plain language - from “all privileged users in finance with unused entitlements” to “all JIT requests in Q2” - and the AI-Agent delivers, instantly.
8. Governance Without Gaps
Tailored risk detects that adapts to your business model, ensuring governance aligns with real-world threats with AI-powered Custom Risk Issues.
Every organization has unique risks. The AI-Agent allows security teams to define custom risk conditions - like separation-of-duties violations between finance and procurement - and continuously monitor for them.
Building Toward Autonomy
Each step of our journey has laid the groundwork for this moment. The AI-assistant gave every user the power to query complex identity data in plain language. The MCP Server opened the door for agents to act safely and intelligently across enterprise systems. Now, the AI-Agent brings true autonomy to identity governance - relieving teams of repetitive decisions, adapting to organizational change, and securing access at business speed.
What’s Next
This is just the beginning. In the coming weeks, we’ll publish deep-dives exploring each capability in action - from how Access Profiles eliminate role bloat, to intelligent and automated review, provisioning and deprovisioning of access.
With the Linx AI-Agent, identity security and governance finally becomes what it was always meant to be: continuous, contextual, and autonomous.
Your identity future starts now.
The Identity Intelligence Awakening: What BlackHat 2025 Revealed About the Future of Enterprise Security
BlackHat 2025 just confirmed what security leaders have been whispering in hallway conversations: traditional IAM is fundamentally broken, and the industry finally has a name for the solution.
After three days at Mandalay Bay, one thing became crystal clear. The cybersecurity industry has reached an inflection point. The conversations happening between sessions, in vendor booths, and during networking events all circled back to the same fundamental challenge: organizations can't secure what they can't see, and most can't see their identity landscape at all.
This visibility crisis has a name now. In its 2025 Hype Cycle for Digital Identity, Gartner introduced Identity Visibility and Intelligence Platforms (IVIP) as an emerging category. But BlackHat revealed that while the industry is just recognizing this need, some organizations are already building solutions that go far beyond basic visibility.
The BlackHat Wake-Up Call: When Simple Questions Have No Easy Answers
The most revealing conversations at BlackHat weren't happening on stage. They were happening when security leaders admitted they couldn't answer basic questions about their own environments.
"Who has admin access to our production AWS accounts?" Simple question. But across multiple vendor demonstrations and client discussions, the same pattern emerged: security teams would need days or weeks to provide a complete answer, assuming they could provide one at all.
BlackHat 2025 showcased the scale of this problem. Presentations highlighted that organizations are dealing with 40:1 machine-to-human identity ratios. AI initiatives are creating thousands of new service accounts, API keys, and autonomous agents daily. Meanwhile, attackers are increasingly targeting identity systems directly, knowing that traditional perimeter defenses can't protect what organizations can't even inventory.
The statistics presented throughout the conference painted a stark picture. With 10.53 billion visits to AI sites in January 2025 alone, the explosion of AI adoption isn't just changing how business operates. It's fundamentally breaking traditional approaches to identity management.
The IVIP Response: Industry Recognition of a Critical Gap
Gartner's introduction of Identity Visibility and Intelligence Platforms as a category validates what BlackHat made obvious: traditional IAM tools weren't designed for today's identity complexity.
As Gartner defines it, IVIPs "gather, categorize, and visualize identity data across directories, tools, and multiple IAM domains." The key insight is that these platforms act as an intelligence layer that makes sense of identity data scattered across environments.
The vendor announcements at BlackHat supported this trend. Multiple companies showcased new capabilities focused on identity visibility, AI-powered access decisions, and autonomous security operations. The market is clearly moving toward platforms that can understand relationships between identities across systems rather than managing them in isolation.
But here's what became clear during the conference: basic visibility, while necessary, isn't sufficient. Organizations need platforms that can not only see their identity landscape but intelligently act on that information.
Beyond IVIP: The Agentic Intelligence Evolution
The most forward-thinking discussions at BlackHat centered on what comes after basic identity visibility. While IVIP addresses the "what can we see" question, the real competitive advantage lies in platforms that can autonomously understand, predict, and act.
This represents the evolution to agentic identity intelligence. Instead of just providing dashboards and reports, these platforms enable security teams to have conversations with their identity data.
Imagine asking "Show me all dormant admin accounts in Snowflake without MFA" and getting an instant, actionable answer. Or having systems that automatically detect unusual access patterns and revoke suspicious permissions before incidents occur. This isn't theoretical. Some organizations are already implementing these capabilities.
The BlackHat demonstrations that drew the biggest crowds weren't showing better visibility tools. They were showcasing platforms that could think, learn, and act autonomously on identity decisions.
Where Linx Leads: Already Built for the Intelligence Era
While the industry catches up to what IVIP represents and vendors rush to rebrand existing tools, Linx has been purpose-built for this exact evolution.
Linx represents what comes after basic identity visibility. It's designed as an agentic identity intelligence platform that delivers the IVIP capabilities Gartner identified while enabling the autonomous decision-making that BlackHat revealed organizations actually need.
Conversational Identity Intelligence: Security teams can ask complex questions in natural language and get instant, actionable answers. No specialized query languages, no waiting for custom reports, no dependency on deep technical skills.
Autonomous Governance: The platform automatically detects policy violations, manages access reviews based on risk context, and maintains audit-ready posture without constant human intervention.
Predictive Risk Assessment: Instead of reacting to incidents, Linx identifies potential security issues before they become problems by analyzing behavioral patterns and contextual anomalies across the entire identity ecosystem.
Intelligent Automation: The system learns organizational approval patterns and automates routine access decisions while escalating only what truly requires human judgment.
What makes Linx different isn't just better visibility into identity data. It's the intelligence layer that turns that visibility into autonomous action, enabling organizations to secure their expanding identity landscape without exponentially increasing their security team headcount.
The Competitive Reality
BlackHat 2025 made one thing undeniable: the organizations that will dominate the next decade are those building identity intelligence capabilities today. While others scramble to implement basic IVIP visibility, leading organizations are already deploying agentic systems that make identity security a competitive advantage rather than a constant struggle.
The window for this advantage won't stay open long. As the industry recognizes what IVIP represents and more vendors enter the space, the differentiation will shift from having identity visibility to having identity intelligence.
For organizations serious about getting ahead of this curve, the choice is clear: implement basic visibility tools and hope to upgrade later, or deploy purpose-built intelligence platforms that are already designed for the autonomous future the industry is racing toward.
The conversations at BlackHat 2025 confirmed what forward-thinking security leaders already knew: the future of enterprise security runs on intelligence, not rules. The question is whether you'll build that intelligence today or implement yesterday's solutions tomorrow.

What Identiverse 2025 was Focusing On This Year (And Where Linx Fits In)
Identiverse 2025 brought together over 3,000 identity leaders in Las Vegas-and it reinforced what many of us in the space have already been working toward: identity is no longer just a tool for access. It’s the foundation of modern security and compliance.
As long-time practitioners in this space, we weren’t surprised by the themes that dominated the keynotes, panels, and hallway conversations. But it was powerful to see the broader industry converging around the same urgent priorities we’ve been building for at Linx.
Here are five of the most important signals that emerged and how our approach at Linx aligns with where the market is heading.
Top 5 Signals from Identiverse 2025
1. AI is Reshaping Identity at Every Layer
AI is no longer a “what-if.” It's actively reshaping how identities are attacked-and defended. Attendees shared how generative AI is powering phishing, lateral movement, and even deepfake-based social engineering. But it’s also accelerating defense: from smarter access reviews to risk-aware automation.
Conference sentiment: Forward-looking. AI is now part of the identity stack, whether we like it or not.
2. Real-Time, Event-Driven Access is Becoming the Standard
The days of quarterly reviews and role-based provisioning are giving way to dynamic, signal-based governance. Triggers like inactivity, org changes, or privilege escalation are being used to adapt access decisions in real time.
Conference sentiment: Overdue. Static access models can’t keep up with today’s cloud velocity.
3. Compliance is Driving Urgency
Between DORA, NIS2, CRA, and evolving expectations from internal auditors, compliance is putting identity in the spotlight. Organizations are under pressure to demonstrate least-privilege, clean up entitlements, and automate certifications-all without slowing business operations.
Conference sentiment: Compliance is no longer a checkbox-it’s a forcing function for modernization.
4. Non-Human Identities Are Now Everyone’s Problem
Multiple sessions highlighted the explosion of NHIs-API keys, service accounts, machine identities-that now outnumber human identities by 20:1 in many enterprises. These identities often live outside of traditional governance programs, creating massive blind spots.
Conference sentiment: High alert. NHIs are no longer niche-they’re core risk.
5. ISPM is Gaining Ground as the New Must-Have
Identity Security Posture Management (ISPM) emerged as a key trend, as organizations look for better ways to continuously assess, manage, and enforce their identity configurations across clouds and SaaS. Unlike legacy tools focused only on provisioning or policy, ISPM bridges the gap between security context and governance workflows.
Conference sentiment: ISPM isn’t a category to watch-it’s the convergence point the industry needs.
How Linx is Already Aligned With This Shift
What many were presenting as future-state aspirations are realities we’ve been delivering on:
- AI-enhanced access control: Linx applies machine learning to reduce review fatigue, automate low-risk approvals, and escalate what truly matters.
- Signal-based policy engine: Our event-driven architecture lets you revoke, escalate, or recertify access dynamically-based on real-world context.
- Audit-ready from day one: We help customers pass audits faster with scoped entitlements, dynamic reports, and real-time visibility across environments.
- NHI-first mindset: Linx doesn’t treat machine identities as an afterthought-we govern them with the same precision as human users.
- Unified security + governance: Our platform combines visibility, decision-making, and enforcement in a single place-exactly what ISPM is meant to be.
What Identiverse 2025 Meant for Linx
For us, Identiverse was a momentum milestone.
We had back-to-back meetings with customers, partners, and practitioners, many of whom validated our direction and pushed for deeper collaboration. The demand for identity-first security solutions is very real-and the market’s readiness for change is accelerating.
The highlight? The launch of the Linx MCP Server-our new lightweight, cloud-native decision point for enforcing real-time access policies across identity providers, SaaS apps, and infrastructure.
It was a hit.
The booth buzz, live demos, and follow-up interest confirmed what we hoped: teams are hungry for elegant, enforceable policy-without the overhead.
From reactive and manual to proactive, intelligent, and automated.
At Linx Security, our mission is to make identity governance and administration both radically intelligent and radically autonomous. That mission just took a major leap forward.
Earlier this year, we introduced the Linx AI-assistant - a powerful natural language interface that lets anyone ask complex identity questions and get clear, actionable answers without writing a single query.
Today, we’re taking the next step forward.
We are excited to announce the Linx MCP Server - a powerful new runtime service that unlocks seamless interactions between large language models (LLMs) and your identity security and governance data. This is more than just a backend update: it's a strategic foundation that transforms the Linx Platform into a truly agentic system - where intelligent agents don’t just observe your environment, they understand, reason, and act.
What is MCP, and why does it matter?
The Model Context Protocol (MCP) is rapidly becoming the standard for connecting AI models to enterprise systems. Originally introduced to bridge the gap between LLMs and external tools, MCP enables structured, secure communication between AI agents and real-world applications, APIs, and databases.
But while others have used MCP to enrich general-purpose agents, Linx is the first to bring it deeply into the heart of Identity Security and Governance.
Our new MCP Server externalizes three powerful capabilities of the Linx Platform:
Deep graph-based visibility, insights and intelligence: Let agents ask and query the Linx Identity Graph to answer any question on the identity data.
- Unified Identity Security and Governance: Give AI agents safe, governed access to sensitive identity actions like human and non-human Identity investigation, risk detection, as well as access profile, JIT access request, and Access Certification.
- Automation and Remediation at Scale: Let agents flag, recommend, or even trigger the cleanup of unused, risky, or unapproved access, as well as secure identity lifecycle management and access governance.
Built for the Agentic Ecosystem
The Linx MCP Server is designed to plug directly into the rapidly expanding world of AI agents. It’s already integrated with the Linx AI-assistant, and now, it allows you to effortlessly set bi-directional integrations with third-party agents like ChatGPT, Claude, and Gemini.
That means your favorite AI copilots can:
- Investigate and remediate human and non-human identity risks more quickly.
- Onboard and off board new employees and ensure they get exactly the access they need.
- Connect to ticketing systems to automate the processing of access requests.
- Get user inputs and send user notification in your messaging solutions.
- Streamline compliance with contextual recommendations and take action when needed.
We're not just making identity security and governance searchable and actionable, we are making it continuous and autonomous.
Start Your Agentic Governance and Security Journey Today
Don't let a lack of personnel slow you down! With Linx MCP, you can automate your processes without running a single line of code. Whether you're removing access to overprivileged accounts or driving a User Access Review campaign to completion, it's never been easier to secure and govern identity.
Try it now and experience how effortlessly you can empower your team and boost your IAM program with an AI-native Identity Security and Governance Platform. Schedule a demo to start your journey toward an agentic identity security and governance program today!

Following My Passion: Joining Linx Security as CTO to Evolve Identity Security
Identity security is broken. And attackers know it.
After more than 25 years in the cyber arena, approaching challenges from different angles and perspectives, one thing has remained clear: identity security is one of the most critical areas in the field—but one where innovation hasn’t kept pace with the evolving threat landscape and business reality.
For years, organizations have struggled to secure identity, not because they weren’t trying, but because the tools they relied on weren’t built for the way modern enterprises operate. Identity is no longer confined to a corporate perimeter. It spans SaaS applications, cloud workloads, privileged accounts, third-party integrations, and an increasingly complex hybrid environment. Yet, the security solutions designed to protect these identities have failed to keep pace.
I’ve seen this challenge firsthand throughout my career - at the Israeli Prime Minister’s Office, at Microsoft, and at Payoneer. And I’ve seen how slow the security industry has been to adapt.
Linx Security is different. And that’s why I’m here.
The Identity Problem No One Wants to Talk About
Enterprise security has undergone a massive shift in the past decade. We’ve moved from firewalls and VPNs to zero trust architectures, cloud-native security, and AI-driven threat detection. Yet, despite all this innovation, identity security has remained stubbornly stuck in the past.
Here’s the reality:
- Most enterprises don’t know who has access to what. Identity data is scattered across countless applications, directories, and systems - leaving security teams with incomplete visibility.
- Access isn’t static - but identity security often is. Enterprises are still using periodic certifications and manual reviews to govern access, while attackers are exploiting identity gaps in real time.
- Legacy solutions weren’t built for today’s cloud-first world. Traditional identity governance was designed for an era of on-prem directories and corporate networks. In today’s decentralized, API-driven ecosystems, these models break down.
The result? Identity is the single largest attack vector today - and the traditional solutions meant to address it are falling short.
Why Linx Security?
Linx Security is solving this problem at its core. Instead of treating identity as just another compliance checkbox, Linx has built an AI-driven platform that continuously maps, monitors, and mitigates identity risk in real time. It provides complete visibility across the modern enterprise—not just who has access, but what they’re doing with it, and what risks that creates.
This is what enterprises desperately need: a way to not just govern identity but to truly secure it—proactively, continuously, and at scale.
Beyond the technology, what truly sets Linx apart is the exceptionally talented team behind it. From world-class security experts to visionary builders, Linx has assembled a group of people who don’t just understand the challenges of identity security—they’ve lived them. What unites them is a shared sense of purpose and a deep commitment to helping customers solve real, urgent problems. The culture here is one of relentless innovation, deep collaboration, and an unshakable drive to make a meaningful impact. It’s a team that moves fast, thinks big, and is driven by a shared mission: to redefine how enterprises secure identity in a world where the old approaches no longer work.
At the heart of it all are the founders—CEO, Israel Duanis, and CPO, Niv Goldenberg—deeply experienced, visionary leaders who have built and scaled security products at the highest levels. What stood out most to me was their deep knowledge of security, their unwavering focus on customers, their ability to build and inspire a world-class team, and their bold approach to innovation. They’ve created a culture where solving real customer problems is the driving force, where top talent thrives, and where big ideas are turned into action.
When I first encountered Linx, it reminded me of the early days of some of the biggest shifts in enterprise security—when companies like Microsoft, Wiz, and CrowdStrike redefined their categories. Linx is doing the same for identity security.
Bringing Enterprise-Scale Security Innovation to Identity
I’ve spent my career scaling security solutions for some of the world’s most complex environments.
At Microsoft, as Vice President of Product & Engineering, I led the integration of CyberX, Aorato, and Adallom into Microsoft’s security ecosystem—transforming best-in-class security technologies into enterprise-ready solutions used by Fortune 500 companies.
At Payoneer, as CTO, I drove platform innovation and system modernization, securing one of the largest global financial infrastructures—enabling businesses to scale securely without compromising compliance.
Now, at Linx, I see a once-in-a-decade opportunity to redefine how enterprises protect identity.
The Future of Identity Security Starts Now
Linx Security isn’t just building another security product. We’re building the future of identity security.
The old ways—reactive identity governance, slow certification cycles, and fragmented visibility—have run its course. Attackers move fast, and security teams need solutions that can move faster.
That’s what we’re delivering at Linx.
I’m excited to be part of this journey—working with a team of security veterans, builders, and innovators to solve one of cybersecurity’s biggest challenges.
If you’re a security leader looking to rethink identity security—or a technologist who wants to help build the future—let’s talk.
Sign up to get new articles & updates from the Linx team sent straight to you.