Identity Governance
Blog posts by category
The State of IGA in 2026
If you’re evaluating identity governance and administration (IGA) solutions in 2026, you already know that the average enterprise has more non-human identities than human ones. At the same time, identity-related breaches continue to rise, and the traditional process of manually reviewing access or defining static roles is simply too slow. A strong IGA platform should handle all of these challenges out of the box.
In this article, we’ll explore the top 10 IGA tools to consider, organized by category, so you can quickly identify what type of platform suits your organization.
IGA Tools Comparison
Modern IGA Platforms
Modern IGA solutions automate the full identity lifecycle and continuously enforce the principle of least privilege across human and non-human identities.
1. Linx Security
At a Glance
Founded: 2023
Headquarters: New York, New York
Category: AI-native IGA & Identity Security
Deployment model: SaaS (cloud-native)
Customer rating: 5/5 on Gartner Peer Insights
Linx - Best for AI-Driven Identity Security and Governance
Linx is best for organizations that want a modern, AI-native IGA solution with fast deployment, real-time governance, and strong automation across both human and non-human identities.
Description and Features
Linx is an AI-native platform that combines deep identity visibility, automated governance, and continuous security enforcement into a single product. At its core is the Linx Identity Graph, which normalizes and correlates data across human, non-human, and agentic identities, mapping the full access path from identity to resource.
The Linx Identity Graph empowers you to make informed decisions: You understand, at a glance, who had access, how they gained it, whether they used it, and the blast radius in the case of a compromise. With a single click, you can remediate the root cause of an issue straight from the Identity Graph.
Linx gives you this full visibility into your identity environment by pulling data from every application and system you use. This full coverage is thanks to an extensive library of out-of-the-box connectors, which also include legacy and on-premises systems that many competitors overlook.
Linx also offers automated access review and remediation workflows that continuously evaluate entitlements and detect drift. When access needs to be adjusted or even revoked, remediation happens directly inside the platform: You don’t need any ticketing loops or manual intervention.
Additionally, Linx has introduced Autopilot, the first AI agent built for identity security and governance. Unlike AI systems that only operate on demand, Autopilot monitors identity environments 24/7, detects changes in real time, evaluates risk in context, and takes action to remediate issues. With Autopilot, you get an always-on, autonomous coverage that eliminates the manual work of chasing access reviews, freeing up security teams to focus on implementing new features rather than firefighting.
The bottom line? With Linx, you get a single solution that covers visibility, governance, lifecycle automation, and identity security without the complexity and cost of legacy IGA vendors.
Pros
- Combines IGA and identity security posture management (ISPM) in one platform.
- AI-native architecture built from the ground up — not a legacy platform with AI bolted on.
- Well-suited for the modern era with strong support for non-human and agentic identities, quick deployment, and industry-leading time-to-value.
- Identity Graph provides unified, real-time visibility across human, non-human, and AI agent identities in a single view.
- Autopilot performs autonomous remediation, not just recommendations. It detects, evaluates, and acts without requiring human intervention.
- In-platform remediation eliminates ticketing loops and manual handoffs.
- Clean, non-technical UI makes the platform accessible to GRC and security personas without developer involvement. No query language needed.
Cons
- Smaller connector library and SI partner ecosystem than legacy IGA leaders.
- On-premises application support is more limited than platforms like SailPoint.
- Fewer community resources, public documentation, and third-party implementation partners.
- As a newer company, Linx has been recognized by Forrester but doesn’t have the same analyst recognition as some of the others.
2. Veza
At a Glance
Founded: 2020
Headquarters: Los Gatos, California
Category: Identity Security
Deployment model: SaaS (cloud-native)
Customer rating: 4.8/5 on Gartner Peer Insights
Veza - Best for Permissions-level Access Visibility
Veza is best for security teams that need deep visibility into permissions and authorization across cloud and data systems, especially across complex data environments like Snowflake, AWS, and custom applications.
Description and Features
Veza's Access Graph maps an organization’s entire identity ecosystem, with a deep focus on data and infrastructure. This approach makes Veza strong for access visibility and least-privilege enforcement.
Recently, Veza has introduced Access Agents, which are AI agents designed for governance tasks. Veza has also invested in AI agent security to provide visibility into MCP servers, AI agent permissions, and LLM infrastructure.
Pros
- Access Graph delivers the most granular permissions visibility in this category — mapping down to specific data objects, tables, and resources, not just users and groups.
- Exceptionally strong for data system governance across Snowflake, databases, and cloud infrastructure.
- 300+ integrations covering cloud, SaaS, and custom environments.
- AI Agent Security product provides visibility into MCP servers, AI agent permissions, and LLM infrastructure.
- Recognized in the 2025 Gartner Market Guide for Identity Governance and Administration.
Cons
- Acquired by ServiceNow in December 2025, meaning product roadmap, pricing, and support structure are subject to change.
- Veza has no true in-platform remediation, meaning it can surface risk but cannot execute remediation without leaving the platform.
- Traditional IGA workflows — access requests, lifecycle management, provisioning automation — are recent additions, not core strengths.
- Less mature for end-to-end IGA compared to vendors built around the full lifecycle from day one.
(Note: ServiceNow acquired Veza in December 2025)
3. Lumos
At a Glance
Founded: 2020
Headquarters: San Francisco, California
Category: SaaS Management IGA
Deployment model: SaaS (cloud-native)
Customer rating: 4.6/5 on Gartner Peer Insights
Lumos - Best for SaaS Access Automation
Lumos is best for mid-market companies focused on automating access requests and approvals across SaaS apps, especially those prioritizing employee self-service and productivity.
Description and Features
Lumos is a modern IGA platform that offers real-time visibility into enterprise SaaS ecosystems and allows companies to automate access requests through channels like Slack. When you connect Lumos to your organization’s cloud applications, it can check and map all user permissions and simplify access requests through a self-service portal.
Pros
- Strong SaaS access automation and self-service workflows.
- Access reviews surface only what has changed since the last cycle, reducing reviewer fatigue.
- Self-service access requests through Slack reduce IT tickets without sacrificing governance.
- Intuitive user experience for business users and employees.
Cons
- Lumos is built around what the IdP knows, not deep, fine-grained entitlements inside each app, resulting in a shallow data model.
- Lumos was built as a SaaS management platform, so support for NHIs and agentic identities is weak compared to competitors.
- Fewer connectors for legacy and on-prem systems compared to enterprise-focused competitors.
- Not well-suited for organizations with complex regulatory compliance requirements or deep ERP governance needs.
4. Opal Security
At a Glance
Founded: 2020
Headquarters: San Francisco, California
Category: Modern IGA & Authorization
Deployment model: SaaS (cloud-native)
Customer rating: Not yet listed
Opal Security- Best for Just-in-Time Access Governance
Opal Security is best for engineering-heavy organizations that want granular, real-time access governance with deep developer tooling integrations and just-in-time access controls.
Description and Features
Opal Security is an authorization reasoning platform with an intelligent data layer that continuously analyzes access behavior across cloud, SaaS, and on-prem environments. Developer-native integrations and a 2025 Risk Layer for AI agent governance round out the platform.
Pros
- Just-in-time access controls convert standing privileges to time-bound grants.
- Developer-native integrations with Terraform, Slack, Jira, PagerDuty, and GitHub make Opal a natural fit for engineering-led security teams.
- AI agent governance is purpose-built.
- In-platform remediation eliminates ticketing loops and manual handoffs.
- Equal support for human and non-human identities.
Cons
- Smaller connector library compared to established enterprise IGA vendors like SailPoint or Saviynt.
- Traditional IGA workflows, including full lifecycle management, ERP SoD enforcement, complex compliance reporting, are less mature than purpose-built governance platforms.
- Not well-suited for organizations with significant on-premises or legacy infrastructure.
- Opal has a smaller partner ecosystem and fewer third-party implementation resources than legacy IGA leaders.
Legacy IGA Platforms
Legacy IGA platforms are traditionally on-premises identity governance tools that rely heavily on manual workflows and static roles. They usually need dedicated teams to deploy and manage them.
5. SailPoint
At a Glance
Founded: 2005
Headquarters: Austin, Texas
Category: Enterprise IGA
Deployment model: SaaS + Hybrid
Customer rating: 4.8/5 on Gartner Peer Insights
SailPoint - Best for Heavy On-prem Enterprises
SailPoint is best for large enterprises in regulated industries that need a battle-tested IGA platform with a mature SI partner ecosystem and the flexibility to run cloud, on-prem, or both.
Description and Features
SailPoint offers AI-powered access reviews, a broad library of connectors, and lifecycle automations. Its strengths are scale and depth, and it can help you govern tens of thousands of identities across a complex hybrid environment.
Pros
- Market leader with 20 years in enterprise IGA and a Gartner Magic Quadrant Leader designation.
- Broad connector library spanning thousands of integrations across SaaS, cloud, and on-prem systems.
- Flexible deployment: SaaS (Identity Security Cloud) and on-prem (IdentityIQ) options supported.
- Large system integrator partner ecosystem for complex global deployments.
- Agent Identity Security product extends governance to AI agents operating in Salesforce, ServiceNow, Snowflake, and more.
Cons
- Implementations are notoriously complex: often 12+ months to reach maturity, with professional services costs that can triple the initial software price.
- Designed for large enterprises with dedicated IAM teams — mid-market organizations often find it oversized and expensive.
- UI is widely considered dated compared to modern cloud-native competitors.
- IdentityIQ and Identity Security Cloud have different feature sets, creating governance gaps for organizations running both simultaneously.
6. Saviynt
At a Glance
Founded: 2005
Headquarters: El Segundo, California
Category: Cloud-first IGA
Deployment model: SaaS
Customer rating: 4.8/5 on Gartner Peer Insights
Saviynt - Best for ERP-heavy Organizations
Saviynt is best for enterprises looking to consolidate IGA, PAM, and Application Access Governance into a single platform, particularly those running complex ERP environments like SAP or Oracle that require strong Separation of Duties enforcement.
Description and Features
Saviynt is a cloud-native IGA platform that provides identity governance and cloud infrastructure entitlement management (CIEM) in a single solution. It has machine learning capabilities, and its built-in IdentityBot RPA engine automates provisioning tasks. It’s a good choice if you want a platform that covers IGA, PAM, and CIEM without having to buy three separate tools.
Pros
- Converges IGA, PAM, and Application Access Governance into a single platform, eliminating the need to buy and integrate separate tools.
- Out-of-the-box SoD rulesets for SAP, Oracle, Workday, Salesforce, and NetSuite, which is a significant advantage for ERP-heavy organizations.
- Five consecutive Gartner Peer Insights Customers' Choice recognitions — the only vendor in this category with that distinction.
- Available on AWS Marketplace for simplified procurement.
Cons
- Steep learning curve and complex initial setup — typically requires a dedicated IAM team.
- Standard contracts are typically structured as three-year commitments.
- Support responsiveness can be inconsistent, particularly during issue resolution.
- Licensing SKU changes have created confusion and unexpected feature gaps for existing customers.
7. Omada
At a Glance
Founded: 2000
Headquarters: Copenhagen, Denmark
Category: IGA
Deployment model: SaaS + On-prem
Customer rating: 4.6/5 on Gartner Peer Insights
Omada - Best for Compliance-heavy Organizations
Omada is best for European enterprises and organizations with strict GDPR, NIS2, or cross-border data residency requirements that need deep hybrid environment support and a strong implementation track record.
Description and Features
Omada Identity Cloud’s best features are code-free configuration, AI-powered analytics, and role-based access control. Omada can be a good choice for mid-to-large companies that need a structured, compliance-focused IGA solution with strong support for hybrid environments.
Pros
- Founded in 2000, meaning Omada has one of the deepest track records in enterprise IGA, with proven deployments in complex hybrid environments.
- Code-free configuration reduces dependency on developers for workflow and policy changes.
- Cloud Accelerator package offers a guaranteed 12-week implementation at a fixed cost, which is rare for IGA vendors.
- Strong European presence with deep expertise in GDPR, NIS2, and cross-border compliance requirements.
Cons
- Smaller community, fewer public knowledge base resources, and fewer third-party integration partners than SailPoint or Okta.
- Feature discovery is not always intuitive — some capabilities are buried under non-obvious menu labels.
- Implementation still requires a meaningful lift; initial performance can lag before the system is fully tuned.
- Troubleshooting import errors and single identity issues can be difficult for administrators.
- Less momentum in North America compared to European markets.
Identity and SaaS Governance Platforms
Identity and SaaS governance platforms prioritize fast deployment and visibility, but they often fall short of full lifecycle management.
8. Okta Identity Governance
At a Glance
Founded: 2009
Headquarters: San Francisco, California
Category: IGA (add-on module to Okta platform)
Deployment model: SaaS
Customer rating: 4.2/5 on Gartner Peer Insights
Okta Identity Governance - Best for Existing Okta Customers
Okta Identity Governance is best for companies already using Okta that want to extend their IAM platform into lightweight IGA with minimal additional tooling.
Description and Features
Okta Identity Governance (OIG) extends Okta’s core identity platform. It leverages Okta’s existing directory and SSO integrations to add lifecycle management, periodic reviews, and audits to verify who has access to what without requiring a separate IGA deployment.
Pros
- The only vendor on this list with publicly listed pricing (~$4/user/month as a standalone add-on; ~$17/user/month in the full Essentials bundle).
- Lifecycle Management, Workflows, and Access Governance share the same data model and admin experience as core Okta.
- Fast time to value for organizations already running Okta as their IdP.
- Strong pre-built integrations across the modern SaaS stack.
Cons
- Not a viable standalone IGA platform — value is almost entirely dependent on existing Okta adoption.
- Limited advanced SoD controls and granular policy engines compared to dedicated IGA vendors.
- Governance capabilities thin out significantly for non-SaaS, hybrid, or on-prem environments.
- Not well-suited for complex regulatory compliance use cases requiring deep entitlement modeling.
9. CyberArk Identity Security Platform (Zilla)
At a Glance
Founded: 1999 (CyberArk) / 2019 (Zilla)
Headquarters: Petach Tikva, Israel
Category: PAM + IGA
Deployment model: SaaS + Hybrid
Customer rating: 4.8/5 on Gartner Peer Insights
CyberArk Identity Security Platform - Best for PAM-first Orgs Expanding into IGA
CyberArk Identity Security Platform is best for organizations that already rely on CyberArk for privileged access management and want to extend modern IGA capabilities through the same platform rather than buying a standalone tool.
Description and Features
CyberArk is known for its robust privileged access management (PAM) capabilities and has expanded to offer broader identity security. CyberArk can help you secure your high-risk credentials (enforcing just-in-time access and recording privileged sessions), and it also provides features like adaptive MFA and identity lifecycle management.
Pros
- Modern IGA via the Zilla acquisition.
- 1,000+ integrations spanning cloud, SaaS, and on-prem environments.
- Just-in-time access with zero standing privileges reduces attack surface across both PAM and IGA workflows.
- AI Profiles capability automates role management using machine learning.
Cons
- Acquired by Palo Alto Networks in February 2026, meaning the product roadmap and pricing are subject to change.
- IGA capabilities are newer and less mature than dedicated IGA platforms. In particular, access request workflows have gaps.
- UI is considered dated by many users compared to modern cloud-native alternatives.
- Platform upgrade stability has been flagged as a concern in user reviews.
- Best fit is PAM-first organizations — pure IGA buyers may find the platform oversized and expensive for their needs.
Note: Palo Alto Networks acquired CyberArk in February 2026.
10. Zluri
At a Glance
Founded: 2020
Headquarters: Milpitas, California
Category: SaaS Management + IGA
Deployment model: SaaS (cloud-native)
Customer rating: 4.6/5 on Gartner Peer Insights
Zluri - Best for Mid-Market SaaS Management
Zluri is best for mid-market companies looking for a simple, SaaS-first IGA solution with strong SaaS discovery and application management capabilities, without the overhead of an enterprise-grade IGA deployment.
Description and Features
Zluri is a SaaS management and identity governance platform that uses its discovery engine to surface all applications in your environment, including shadow IT. This comprehensive visibility enables IT and security teams to see exactly which tools are being accessed and by whom, providing a strong foundation for governance and cost optimization.
Pros
- Nine-method discovery engine surfaces all applications in an environment, including shadow IT, which is one of the most comprehensive SaaS visibility approaches in this category.
- IGA and SaaS spend management in one platform. Access governance and license cost optimization are addressed together.
- Sub-hour JML processing means that new hire provisioning and offboarding happen in minutes, not batch cycles.
- Supports access reviews across multiple IdPs (Azure AD, Google Workspace, Okta, JumpCloud) simultaneously.
- Well-suited for mid-market organizations that want SaaS control without enterprise-grade complexity.
Cons
- Policy enforcement and compliance capabilities are less mature than dedicated IGA platforms.
- Feels more like a SaaS management tool with governance features than a governance platform with SaaS management — an important distinction for compliance-driven buyers.
- Not well-suited for organizations with complex regulatory mandates, deep SoD requirements, or significant on-prem infrastructure.
- The feature set is still maturing for enterprise-scale IGA use cases.
Frequently Asked Questions
What is the difference between modern IGA and legacy IGA?
Modern IGA platforms are cloud-native, AI-driven systems that continuously govern identity access in real time, while legacy IGA platforms are on-premises tools built for periodic, manual governance. Legacy platforms rely on scheduled access reviews, manual provisioning, and dedicated engineering teams. Modern IGA replaces that model with continuous monitoring and automated remediation that scales across human, non-human, and AI agent identities, with faster deployment and lower total cost of ownership.
Which IGA platforms support AI agent governance?
Several IGA platforms have introduced AI agent governance capabilities, including Linx, Veza, Opal Security, SailPoint, Saviynt, and CyberArk. Linx governs AI agents and offers continuous drift monitoring. Veza (now part of ServiceNow) provides visibility into MCP servers and LLM infrastructure. Opal Security has introduced a Risk Layer specifically for agentic authorization requests and ships a native MCP server for AI-driven access automation. SailPoint has extended governance to AI agents in Salesforce, ServiceNow, and Snowflake. Saviynt and CyberArk have expanded non-human identity coverage to include agent credentials.
What is the difference between SaaS IGA and on-premises IGA?
SaaS IGA is a cloud-hosted service managed by the vendor; on-premises IGA is software installed and maintained on your own infrastructure. Most modern IGA vendors have moved exclusively to SaaS; legacy platforms like SailPoint IdentityIQ remain available on-premises for organizations with strict data sovereignty requirements.
Does my company need IGA if we already use Okta or Microsoft Entra?
Okta and Microsoft Entra are identity providers that handle authentication and basic lifecycle management, but they are not full identity governance platforms. IGA addresses a complementary set of problems: enforcing least privilege, automating access reviews, managing separation of duties, and governing non-human identities. Both Okta and Microsoft offer governance add-ons, but organizations with hybrid infrastructure, complex compliance requirements, or applications outside those ecosystems typically need a purpose-built IGA platform.
Which IGA platforms are best for mid-market companies?
For mid-market organizations, the best-fit platforms prioritize fast deployment and low operational burden: Lumos, Zluri, Linx, and Opal Security are strong options that deliver value without a dedicated IAM team.
Which IGA platforms are best for large enterprises?
For large enterprises in regulated industries, SailPoint, Saviynt, and Linx offer the compliance automation, ERP integration, and hybrid environment support that complex organizations require.
Do IGA platforms require professional services to deploy?
It depends on the platform and the complexity of your environment. Legacy platforms like SailPoint IdentityIQ almost always require vendor-led or partner-led professional services, with implementations taking 6 to 12 months and services costs that can match or exceed the software license. Modern cloud-native platforms like Linx, Lumos, and Zluri are designed to reduce or eliminate that dependency. When evaluating vendors, ask whether professional services are required or optional and whether implementation costs are included in the platform fee.
What are the top IGA tools in 2026?
The top IGA tools in 2026 fall into three categories. Modern platforms include Linx Security, Lumos, Veza (now part of ServiceNow), and Opal Security. Established enterprise platforms include SailPoint and Saviynt, which offer deep compliance automation at the cost of implementation complexity. Okta Identity Governance, CyberArk (which acquired Zilla Security in 2025 and was acquired by Palo Alto Networks in 2026), Omada, and Zluri round out the category with strengths in ecosystem integration, privileged access, European compliance, and SaaS management respectively.
What should I look for when evaluating IGA vendors?
The most important factors when evaluating IGA vendors are deployment speed, AI capability, connector coverage, and total cost of ownership. Ask whether the platform requires professional services or can be deployed by your internal team. Distinguish between AI-native platforms and those with AI bolted onto a legacy system. Get the full TCO picture including licensing, implementation, and any features charged separately. Lastly, analyst recognition from Gartner or Forrester provides a useful independent quality signal.
Conclusion
In 2026, the direction of the IGA market is clear: Speed, AI-native automation and augmentation, in-platform remediation, and out-of-the-box integrations are now non-negotiable. The best modern IGA tools combine these features with full visibility and intuitive identity lifecycle management.
This is where Linx Security leads the pack. Linx provides full identity governance and immediate time-to-value through its zero-configuration connectors across cloud, SaaS, and on-prem environments. It’s purpose-built for ease of use: You don’t need professional services to deploy or operate Linx.
Better yet, Linx offers round-the-clock, AI-driven coverage so that no identity issues fall through the cracks. Linx Security’s Autopilot continuously analyzes identity risks and auto-remediates policy violations before they become security incidents.
If you are reviewing IGA vendors, read this blog to understand what are the 10 questions you need to ask when evaluating IGA solutions.
At the same time, if you’re looking for an IGA platform that checks all of the boxes, book a demo with Linx Security to experience what an industry-leading IGA can do.
User Access Reviews (Access Certifications): Why They Fail and How to Fix Them
Introduction
As identity-based breaches continue to rise and access misuse becomes a primary attack path, organizations rely on User Access Reviews (UARs) to answer two seemingly simple questions: Who can access what, and should they still be able to?
In theory, this is where stale access should be caught. In reality, it often slips by unnoticed.
Consider a common scenario: A sales operations manager moves into a revenue analytics role. Months later, during a quarterly access review, their new manager is asked to approve continued access to Salesforce admin permissions, Snowflake read access, and a legacy CRM role labeled “SalesOps_Admin_v2.” Faced with dozens of similar decisions, tight deadlines, and little context, the manager approves everything. The review is completed on time. The access persists.
As a result, risk compounds quietly. If an attacker later compromises the account, those lingering admin permissions provide a direct path into sensitive systems, and the activity may appear legitimate because the access was formally approved. By the time unusual behavior is detected, the damage may already be done, hidden behind what looks like valid access.
This article takes a closer look at what User Access Reviews are, why they often fail in enterprise environments, and what actually improves them, including how teams can evolve beyond periodic certification to continuous identity governance.
What Are User Access Reviews and Why Do Organizations Use Them?
User Access Reviews, sometimes referred to as Access Certifications, are formal review processes used to confirm that individuals retain the right level of access to systems, applications, and data.
In modern environments, access needs change constantly. People join teams, move roles, take on short-term projects, and leave. Systems are added, deprecated, or reconfigured. Without a mechanism to revisit access decisions, privileges tend to accumulate.
UARs counter that drift before it turns into persistent risk, making them a key control for security and compliance programs. Security teams rely on them to reduce unnecessary access, regulators expect them, and auditors ask for evidence.
But UARs are much more than box-checking exercises: They’re crucial for combatting the consequences of outdated/over-permissive access, which include an increased blast radius, lateral movement opportunities, and data exposure. Left unchecked, excessive access can also undermine segregation of duties, increase the likelihood of insider misuse, and complicate incident response when permissions are overly broad or poorly documented.
What Do You Actually Review During a UAR?
On a technical level, a User Access Review usually evaluates three core elements:
- First, the user or identity. This may include employees, contractors, service accounts, or other non-human identities. Reviewers need to understand who the identity represents and their current role.
- Second, the application or system. This could be a SaaS tool like Jira or Workday, a cloud service such as AWS, or an internal application. Each system has its own access model and risk profile.
- Third, the entitlements or permissions. These are certain roles, groups, or privileges granted, such as “Jira Project Admin,” “AWS IAM PowerUser,” or “NetSuite AP Clerk.”
A typical review asks an approver to confirm whether each combination of user, system, and entitlement is still required. Teams often formalize this process using a standardized User Access Review checklist to ensure reviews are consistent across systems.
How Are UARs Usually Run?
Most organizations run User Access Reviews as periodic campaigns on a quarterly, semiannual, or annual basis. Security or identity teams first collect access data from identity providers, SaaS applications, and cloud platforms. The data is grouped by user or application and routed to managers, application owners, or both, depending on the organization’s review model.
In manager-led reviews, line managers are asked to certify all access for their direct reports. In application-owner models, system owners validate entitlements for all users of their application. Two-tier approaches combine both, often starting with the manager and escalating higher-risk access to application owners.
In many enterprises, these reviews are still driven by spreadsheets exported from systems that are then emailed to reviewers, tracked manually, and reconciled at the end of the cycle. Evidence is archived for audit purposes.
This model made sense when environments were smaller and change was slower. Today, it struggles to keep up.
Why Do User Access Reviews Break Down in Practice?
In most enterprises, access reviews fail not because teams ignore them but because the process buckles when it meets real-world complexity.
Specifically, ineffective UARs are defined by a lack of context, unclear ownership, a “rubber-stamping” mentality, suboptimal evidence collection, and a lack of real-time coverage.
Why Is There So Little Context in Reviews?
The most common UAR failure mode is a lack of context. Reviewers are asked to make decisions without understanding what the access enables.
A manager reviewing access for an engineer might see roles like “AWS_ReadOnly,” “AWS_PowerUser,” and “CustomPolicy_ProdOps.” Without visibility into what those roles allow or how they are used, the safest path becomes approval.
Who Actually Owns Access Decisions?
Ownership ambiguity compounds UAR's other failure points. In many enterprises, it’s unclear who is accountable for access: managers, application owners, or security teams. This can lead to access decisions that are delayed, inconsistently applied, or approved without meaningful inspection.
Manager-only reviews are common, but managers may not understand application-specific permissions. App-owner reviews improve technical accuracy, but app owners may not know whether access matches a user’s role.
Organizations that require approval from both the manager and the application owner improve coverage but also increase friction and review fatigue.
Why Do Reviews Turn Into Rubber Stamping?
Faced with long lists and tight deadlines, many reviewers default to approving everything. After all, reviewers are rarely rewarded for revoking access, but they are penalized socially or operationally when revocations cause disruption. Over time, this creates a culture in which UARs are seen as a compliance chore rather than a security control.
What Makes Evidence Collection So Hard?
Collecting access data across SaaS, cloud, and on-prem systems is difficult. Entitlements change. Integrations fail. Access lists go stale before reviews start. This means data is often inaccurate, incomplete, or inconsistently labeled.
Inaccuracies can be introduced downstream as well. After the review, teams must package evidence for auditors: who reviewed what, when decisions were made, and what actions were taken. In spreadsheet-driven workflows, this is a manual and error-prone process.
Why Is the Security Value So Short-Lived?
Even when reviews are completed carefully and on time, their impact fades quickly in dynamic environments. As we’ve seen, access changes every day as people switch roles, join new projects, or gain temporary permissions that are never revisited.
By the time a quarterly or annual review is finished, parts of it are already outdated. New access has been granted, old access has lingered, and the risk profile has shifted. The end result? Point-in-time reviews reassure auditors but only provide limited, short-lived protection for the organization.
What Actually Improves UARs?
For many teams, improving reviews means rethinking the tools they rely on. Modern User Access Review software shouldn’t just collect approvals; it should help reviewers understand risk, usage, and context in a single place. This is how organizations can start to automate User Access Reviews without sacrificing decision quality.
To understand the difference robust tooling makes, let’s walk through the principles that actually improve reviews:
- Full Context: In a mature enterprise UAR cycle, access data is normalized across SaaS, cloud, and internal systems so reviewers aren’t working from fragmented exports. A manager reviewing an engineer’s access can see their current role, recent access usage, and whether permissions are common for peers in similar roles. For high-risk systems, application owners are brought in when technical judgment is required.
- Iterative Improvements: When revocations happen, they aren’t treated as one-off cleanups. They become signals. If multiple users lose the same entitlement, that role definition is likely too broad. If access lingers after role changes, joiner-mover-leaver workflows need to be adjusted. Over time, this feedback loop reduces review volume and improves the quality of upstream access.
- Cross-Team Alignment: Security and business teams need a common understanding of what access means and why it matters. Without that shared understanding, reviews become mechanical exercises rather than informed risk decisions.
Taken as a whole, these patterns explain why minor process tweaks tend to have limited impact. Real improvement comes from an approach that scales as the organization evolves.
How Does Linx Security Approach User Access Reviews?
Linx Security treats UARs as an integral part of continuous identity management, shifting teams from reactive certifications to proactive risk reduction.
Here’s how:
- Holistic Coverage: Linx is designed to secure every type of identity, both human and non-human: With Linx, enterprises manage employees, service accounts, automation, and AI agents.
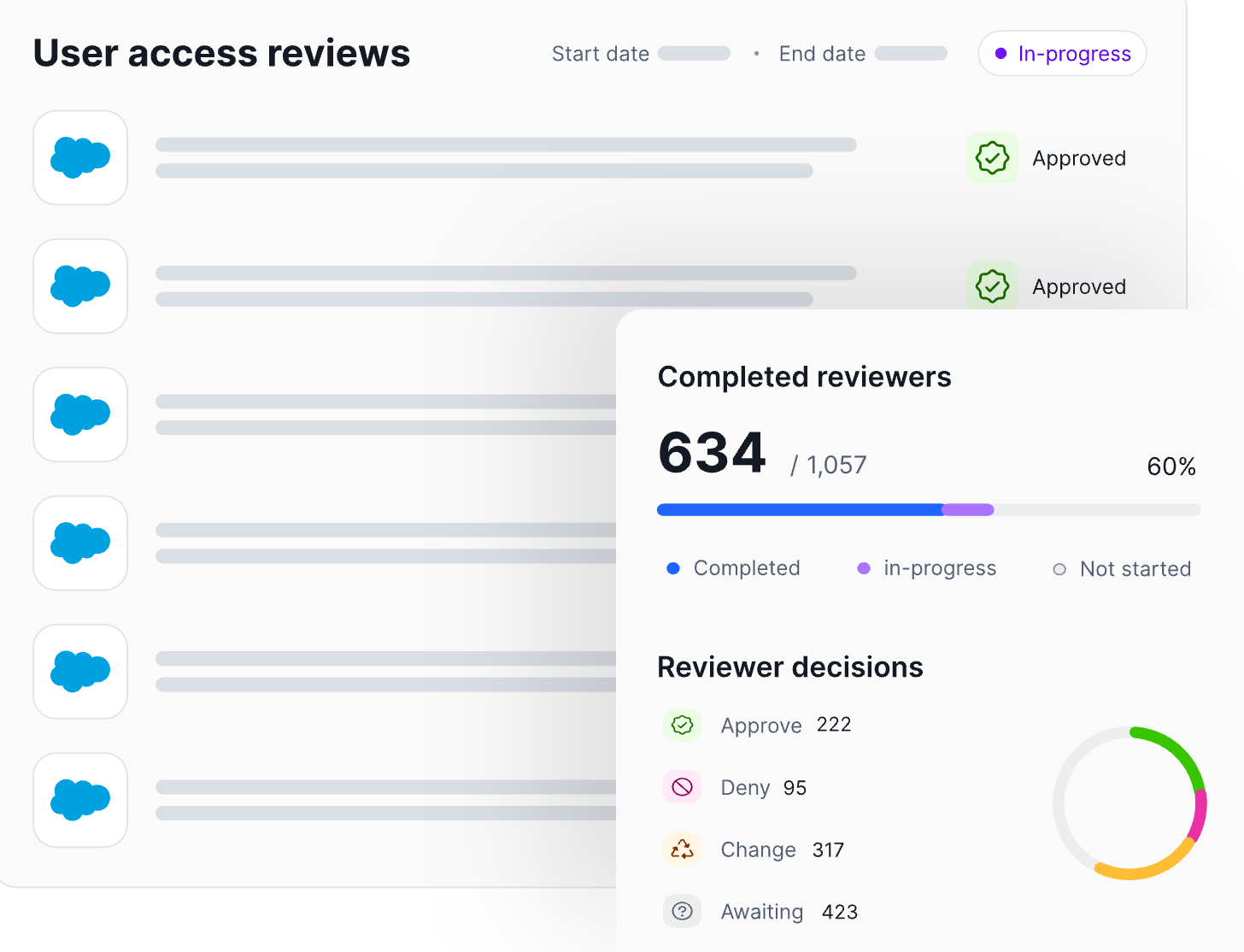
- Automation: Linx automates governance processes to decrease operational burden. For example, Linx can automatically remove or revoke access once a reviewer approves the change, ensuring that decisions made during the review process are executed immediately and consistently across connected systems. Workflows, tracking, and evidence collection are automated end to end. Review decisions are logged as they happen, creating audit-ready evidence by default.
- Context From a Single Pane of Glass: Reviewers see identity attributes, role context, access usage, and risk signals together, guiding smart access decisions.
How Are Linx UARs Intelligent?
Most review processes treat all access the same, regardless of risk or usage. Linx starts from the opposite premise: Not all permissions matter equally.
Linx replaces access lists with clear recommendations that help reviewers focus on decisions that actually reduce risk (such as identifying unused admin roles or access that violates least-privilege expectations).
Access profiles in Linx group related permissions together so reviewers can evaluate access at the profile level rather than reviewing many individual entitlements:
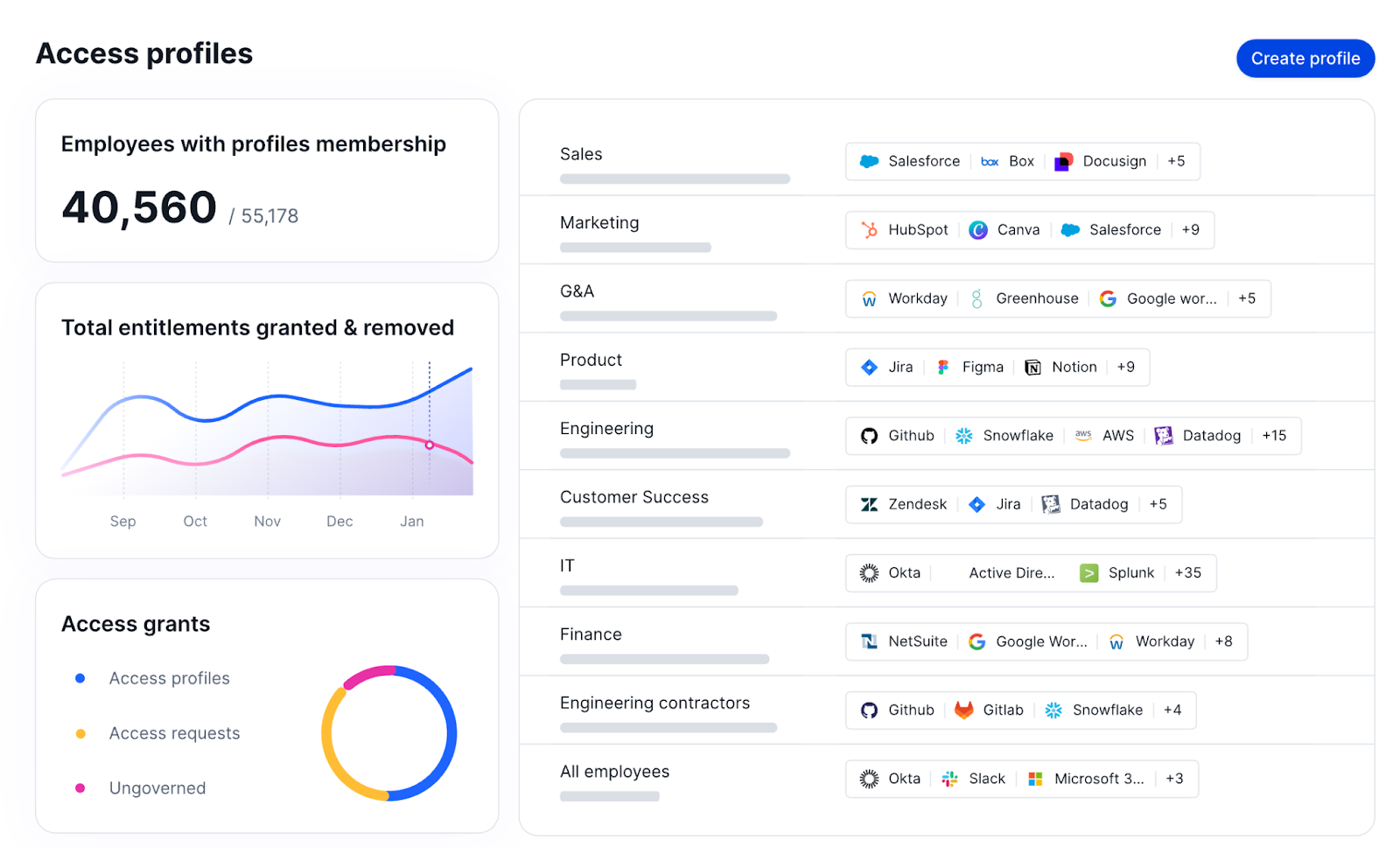
What Does Continuous Governance Look Like?
Continuous governance shifts the role of access reviews. Rather than serving as the primary control, reviews act as a validation step on top of ongoing monitoring and remediation.
“Ongoing” is the key word here. Linx continuously monitors access as it changes. Rather than letting risk accumulate until the next scheduled certification cycle, Linx flags risky access combinations, unused privileges, and newly elevated roles in real time.
The Linx MCP Server exposes governance actions through policy-driven automation interfaces, allowing identity teams and automated tools to remove excessive or outdated permissions when they no longer align with role expectations or governance policies.
The main takeaway? Linx empowers teams to remediate issues immediately or queue them for review, instead of only uncovering them during a scheduled review months later.
In practice, this means UARs become shorter, more targeted, and easier to defend. Auditors still get clear certification records, but those records are backed by continuous monitoring and remediation, not last-minute cleanup.
Conclusion
As environments grow more complex and identity becomes the primary security perimeter, point-in-time certifications alone are no longer enough. Organizations that rely solely on periodic reviews will continue to struggle with rubber stamping, incomplete context, and access that drifts out of alignment with real-world roles. The best IGA solutions, like Linx, automate access reviews and provide real-time visibility and governance.
The path forward isn’t eliminating UARs. It’s strengthening them with context, automation, and continuous oversight so reviews become informed validation checkpoints rather than large-scale cleanup exercises.
If you want to see how continuous identity governance changes the equation, request a demo to experience Linx’s approach to User Access Reviews.
What Are Identity Governance and Administration (IGA) Solutions and Why Are They Important?
Identity governance and administration (IGA) solutions manage the lifecycle of user identities and their permissions across an entire organization, providing full coverage for on-premises, cloud, and hybrid environments. With IGA, you can control who has access to which systems, enforce policies, and provide audit trails.
IGA is critical for security. Within an organization, the number of identities can easily reach into the thousands. Employees, contractors, partners, service accounts, and principals may have access to dozens or hundreds of applications.
Without proper governance, overprivileged access can lead to breaches at scale. Attackers just need access to a single overprivileged account, and then they can move laterally until they hit the systems they’re interested in. (Read our article about the anatomy of an identity breach to learn more.)
How Do IGA Solutions Work?
At the core of IGA is identity lifecycle management (ILM), which is the end-to-end process of managing identities from creation and modification (for role changes) to deletion. User lifecycle management is a subset of ILM that focuses on human identities, but modern platforms extend lifecycle management to non-human identities as well.
One important note: Most IGA tools are not security tools; they’re IT administration tools built to address provisioning and lifecycle management problems. A security-first IGA solution like Linx Security evaluates every entitlement, making it easy to understand the potential damage it could cause.
What Are the 10 Questions to Ask When Evaluating IGA Solutions?
Asking targeted questions is the best way to determine whether the IGA tool you’re considering will strengthen your security posture. The right questions center on the common failure points for IGA solutions, not the checkbox features every vendor supports.
Below, you’ll find a structured framework for the top 10 questions that truly matter. Each section includes context for why the question is important, real benchmarks for good and bad answers, and a discussion of how tools that fall short can lead to vulnerabilities.
1. How Easy Is It to Provision and Deprovision Accounts?
- Why Does This Matter?: In large organizations, accounts are provisioned and deprovisioned daily. Orphaned accounts (active accounts that no longer belong to anyone) are one of the most common entry points for attackers.
- Good Answer: Provisioning and deprovisioning are done automatically through your identity access and governance process. When a new person joins, their account is created with the appropriate access based on their role. Additional permissions can be requested through a self-service portal, which the security team evaluates. When somebody leaves the team, every account across all applications is disabled and removed the same day. Role changes trigger automatic access adjustments.
- Bad Answer: All provisioning and deprovisioning requests rely on manual tickets. IT teams add access for new users step by step, and when someone leaves, the spreadsheet gets updated.
- Impact: Spreadsheet-based workflows can fall through the cracks. Six months after someone’s left, their orphaned account might still have broad access, which is an invitation to attack.
2. What Is the API Coverage for the IGA Solution?
- Why Does This Matter?: The IGA solution you choose needs to integrate with your cloud providers, SaaS applications, HR platform, and ticketing systems.
- Good Answer: The IGA solution is API-first, with all functionality available via the API, including provisioning, deprovisioning, policy management, and even reporting. Implementing custom integrations shouldn’t be a tedious process; it should be easy out of the box.
- Bad Answer: The API is limited to read-only operations or offers only a fraction of what the UI can do. It’s possible to implement custom integrations, but it’s a complex process.
- Impact: With limited API coverage, you can’t really implement automation. There will be delays and misconfigurations, which translate into access gaps that expand your blast radius.
3. What AI/ML Capabilities Does the Platform Have?
- Why Does This Matter?: Manual governance is unsustainable, and AI and ML capabilities can reduce the burden on reviewers and even surface risk.
- Good Answer: The IGA solution uses AI to analyze access patterns, detect anomalies, and make recommendations that reviewers can act on.
- Bad Answer: The IGA solution is “AI-powered,” but it only offers a basic rule engine with no feedback loop.
- Impact: If your IGA solution can’t show you the blast radius of a compromised identity, it’s not actually using AI; it’s a buzzword.
4. What Expertise Is Needed to Get Value Out of the IGA Solution?
- Why Does This Matter?: If you need a large, dedicated team to manage the IGA solution, it will slow you down more than it helps.
- Good Answer: The platform is designed so that identity and security teams can operate it without being experts.
- Bad Answer: You need certified consultants to manage your platform.
- Impact: If operating the platform is too hard or expensive, nobody will update the rules, leading to vulnerabilities. For example, stale access policies can allow former employees to retain permissions they shouldn’t have.
5. Can the IGA Solution Model Complex Environment Relationships?
- Why Does This Matter?: In large enterprises, permissions aren’t flat. They involve nested groups, inherited roles, and service accounts that have chained permissions.
- Good Answer: The IGA solution uses a graph-native model to represent data relationships. An identity graph makes it easy to traverse complex access paths and understand dependencies.
- Bad Answer: The platform uses a relational database that stores access as row-level associations. You can understand that a user has a role, but there’s no context for why that role is dangerous.
- Impact: Without a graph model, blast radius is a permanent blind spot.
6. What Is the Operational Overhead?
- Why Does This Matter?: If you need to pay 5–10 engineers just to manage day-to-day operations, you don’t have an IGA solution; you have IGA overhead.
- Good Answer: A small team of 1–3 engineers is enough to manage the IGA solution. Connectors are maintained by the vendor.
- Bad Answer: The IGA solution needs a dedicated team, and for each new application, you need to implement a manual connector configuration.
- Impact: A team that spends more than half its time keeping the lights on is firefighting instead of focusing on implementing new features.
7. How Can You Deploy the IGA Platform (SaaS, On-Prem, Hybrid)?
- Why Does This Matter?: When you need speed, SaaS solutions are the best fit. Yet for highly regulated industries, on-prem is more suitable. An IGA solution must account for both. Depending on your compliance and speed requirements, you should be able to choose where you deploy your IGA platform.
- Good Answer: You have the flexibility to deploy the IGA platform wherever you want.
- Bad Answer: You can deploy the IGA tool in on-premises or SaaS environments, but there are critical differences between the solutions (e.g., the SaaS version has more features than the on-prem one because it relies on existing cloud services).
- Impact: Without feature parity across deployment models, on-prem customers will receive a second-class experience. At the same time, if you start with SaaS and later want to migrate to on-prem, you’ll need to sacrifice some features in order to make the switch.
8. How Many of My Apps Have Production Connectors Today?
- Why Does This Matter?: There’s a big difference between an app that’s “supported” (meaning you might need a dedicated team to integrate it) and a production-ready connector that’s available right now.
- Good Answer: The IGA solution has a transparent connector catalog that shows exactly which applications have production-ready connectors.
- Bad Answer: The IGA solution claims to have more than 100 built-in connectors, but for half of them, you need to implement custom solutions.
- Impact: If your IGA solution can’t connect to an application, you can’t see the available access. These gaps dramatically increase your attack surface.
9. What Happens When a Review Decision Is Revoked?
- Why Does This Matter?: Every IGA solution can create tickets when access is revoked, but this is a risky default. Tickets pile up, and they can take several days to be implemented.
- Good Answer: When access is revoked, the IGA solution automatically executes the revocation through its connectors. Remediation is tracked, verified, and auditable. This is what a mature IGA solution looks like.
- Bad Answer: The IGA platform generates a ServiceNow ticket that goes into a queue, and someone implements it when they have time.
- Impact: The time between a revocation decision and the actual implementation is pure risk exposure.
10. Can a Reviewer See Why Access Is Flagged Without Opening Another Tool?
- Why Does This Matter?: Toggling between several applications to analyze access is inefficient and overloads engineers.
- Good Answer: The IGA solution is graph-based, meaning the reviewer can understand why the access is flagged at a glance. They never need to leave the platform.
- Bad Answer: The reviewer needs to check several tools to understand why access has been flagged.
- Impact: Friction can lead to a culture of rubber-stamped access permissions.
How Linx Revolutionizes IGA
Traditional IGA solutions were built for compliance, not security. Linx is different.
With Linx, you get an AI-native, security-first IGA solution. All of Linx’s features are purpose-built to give identity teams the visibility and context they need to reduce the blast radius of every identity in your organization.
Linx uses a graph-powered architecture to map every identity to every permission, resource, and relationship across your environments. It offers out-of-the-box automated remediation and a faster time to value with pre-built integrations and no-code connectors.
And with Linx Autopilot, teams can now deploy AI agents that work continuously on their behalf. Autopilot monitors identity environments 24/7, detects meaningful changes, evaluates risk in context, and takes action in real time.
Conclusion
Identity governance and administration solutions ensure that the right people have access to the right resources. Because a single over-privileged identity can become an entry point for a full-scale breach, the IGA solution you choose should be a security control that shows you exactly how large your blast radius is when an attack happens.
If you are ready to start selecting an IGA platform but don't know where to start, check out our blog post on the top IGA tools.
The 10 questions in this article help you separate IGA solutions that look good on paper from vendors that actually secure identities in practice. They empower you to make a choice that slashes risks and provides immediate value.
That’s where Linx stands apart.
If you’re ready to see what AI-native, graph-powered IGA looks like in practice, request a demo of Linx.
Explicit Sharing, Implicit Availability, and Administrative Impersonation
Automation platforms rely on credentials to execute actions under a user’s identity. In n8n, credentials are created by individual users and are commonly perceived as personal, especially when they live in a user’s personal project and aren’t explicitly shared.
In a multi-user n8n instance, though, “who created the credential” and “who can use the credential” are not always the same thing. Credential availability is governed by several mechanisms. Some are explicit and intentional. Others are implicit and easier to miss. The difference matters because it directly impacts identity use, accountability, and auditability.
The observations described here are based on direct experimentation in the n8n Cloud environment.
Credential sharing models in n8n
n8n provides multiple ways in which credentials can be used by users other than their creator. These mechanisms differ in consent, visibility, and scope.
Explicit credential sharing
A credential owner can explicitly share credentials:
- With specific users
- With specific projects
Once shared, other users can execute workflows using those credentials.
This model is straightforward: the owner makes an intentional sharing decision, and other users gain access within the boundaries of what was shared.
Implicit credential availability
In addition to explicit sharing, credentials may be usable by others through implicit relationships.
Implicit case 1: Project-wide credential usage
If user A (member or admin) creates credentials in a project, other members of that project can execute workflows using those credentials, acting on behalf of user A.
This applies even if the credentials were not explicitly shared with each individual member.
In this case, credential usage remains scoped to the project, but the key detail is that “created in the project” can function like “available to the project,” even when individual user-to-user sharing never happened.
Implicit case 2: Instance admin usage across personal projects
A user can create credentials in their personal project and avoid sharing them with any other user or project.
Despite this, an instance admin can:
- Create a workflow in the admin’s personal project
- Select the user’s personal, unshared credentials
- Execute workflows using those credentials
This does not require:
- Credential sharing
- Shared project membership
- Notification to the credential owner
- Additional consent
In other words, credentials created in personal projects are still usable at the instance level by administrators. Practically, “personal” describes where the credential is stored, not who ultimately controls its use.
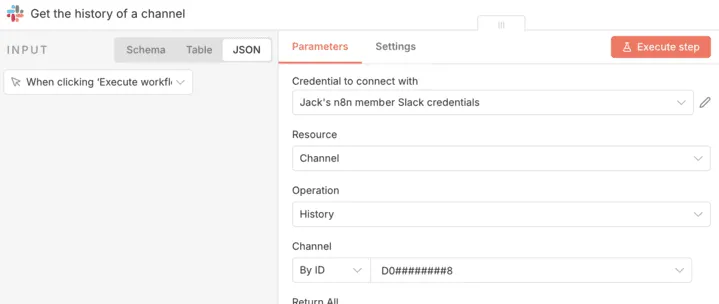
OAuth example: Slack credential reuse
OAuth-based integrations make this behavior especially observable because consent is usually visible to the user.
Here’s the sequence:
- A user authorizes n8n to access Slack via OAuth
- Tokens are issued under the user’s identity
- Credentials are stored in the user’s personal project
- The user executes workflows using those credentials
- An instance admin creates a workflow in the admin’s personal project
- The admin selects the user’s Slack credentials
- No OAuth re-consent occurs
- The user is not notified
- The workflow executes
- Actions occur under the user’s identity
Jack, a member of the organization, creates Slack credentials scoped to his personal project.
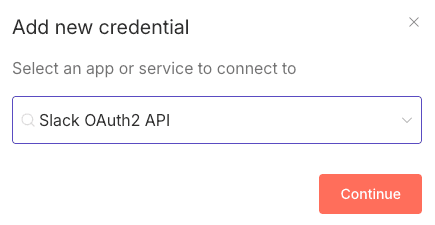
Jack does not share his credentials with anyone:

Jack approves the scopes:

Later on, the instance admin’s own credential set is visible and does not include credentials for Slack.

When the admin creates a new workflow in the admin’s personal project and adds a Slack node, the list of available credentials includes credentials created by other users. Among them are credentials created by Jack, a member of the organization, which were created in Jack’s personal project and not explicitly shared.
The admin can select Jack’s credentials and execute the workflow.
When the workflow is run by the admin, using Jack’s credentials, the resulting data corresponds to Jack’s Slack context. In an experiment we conducted, this allowed the admin to access sensitive information from Jack’s Slack channels, including messages containing salary-related information.
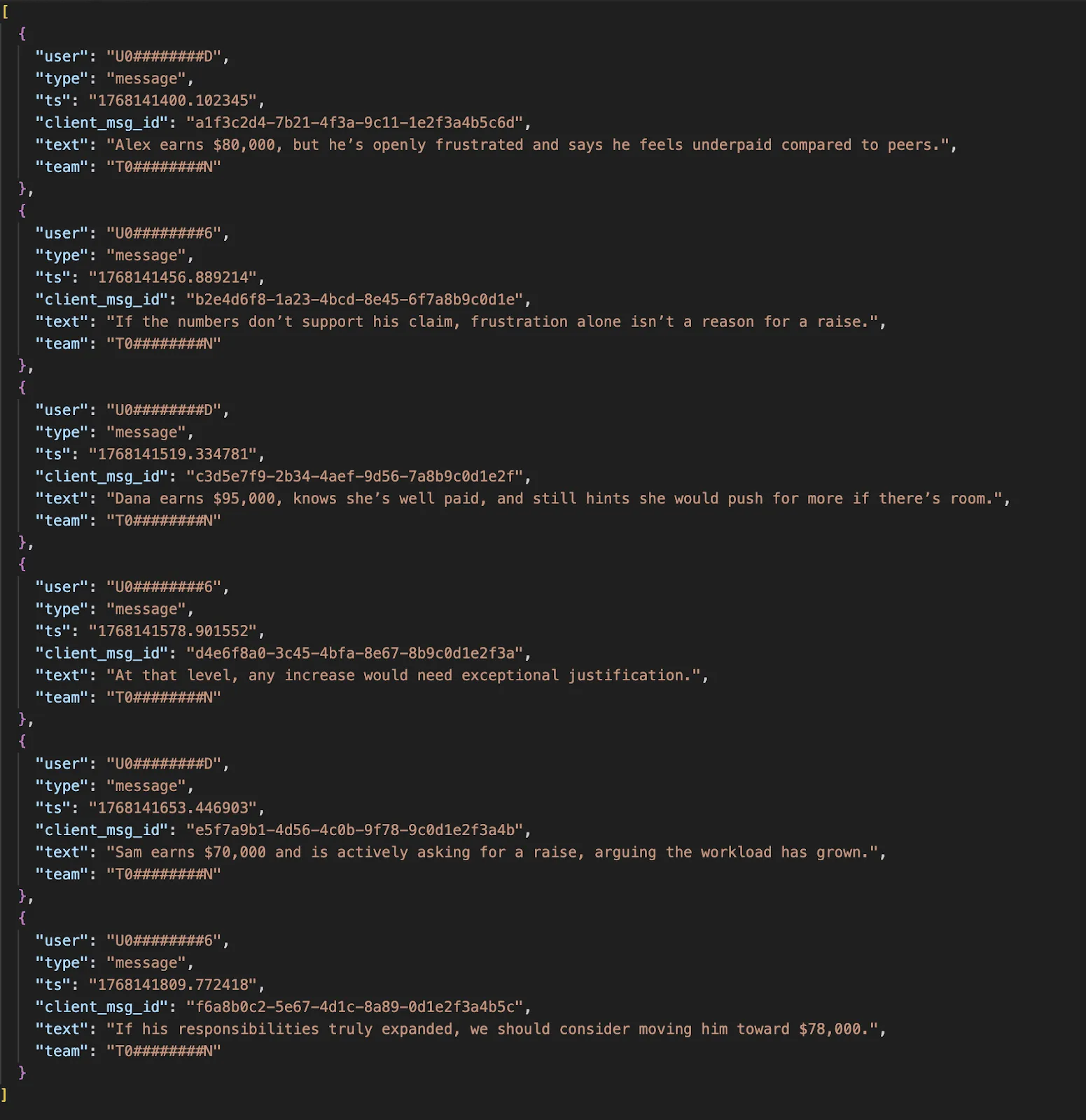
From Slack’s perspective, there is no distinction between actions initiated by the user and actions initiated by an admin using the user’s credentials.
What we validated in practice
In our test, an instance administrator was able to create a separate workflow and run it using another user’s Slack OAuth credentials that were stored in that user’s personal project and not explicitly shared. The workflow executed successfully without re-consent and without alerting the credential owner.
This is the core point: an admin can operationally “become” the user inside downstream systems, because downstream systems only see “valid token for user X,” not “who clicked run in n8n.”
n8n documentation and credential control
n8n states in its public GitHub repository:
“Instance owners and instance admins can view and share all credentials on an instance.”
That statement accurately describes administrative visibility and sharing capabilities.
What it does not explicitly state is that instance admins can execute workflows using credentials created by other users, including credentials stored in personal projects and not shared.
“View and share” and “run as the user” are materially different operations. The former suggests administrative oversight. The latter enables administrative impersonation in downstream systems.
Implications
This model introduces several effects that are easy to underestimate:
- Actions are attributed to the credential owner. Downstream logs reflect the user whose token is used.
- Credential owners cannot distinguish their actions from those performed by admins using their credentials.
- OAuth consent granted by a user applies beyond that user’s control. The token’s effective authority can be exercised by others.
- Credential boundaries align with instance authority rather than user intent. “I didn’t share it” is not the same as “nobody else can use it.”
These effects result from the credential availability model, not from a vulnerability or misconfiguration.
Trust model
n8n’s design assumes that instance administrators are trusted to operate using any credentials present in the instance.
In some environments, that assumption is acceptable. In others, especially those with shared administration, separation of duties, strict audit requirements, or regulated workflows, it may not match organizational expectations.
If your internal model is “admins manage the platform but cannot act as end users,” n8n’s behavior conflicts with that model.
Why this matters for agentic governance
Agentic governance has become an increasingly important issue. Automation tools are increasingly used as execution layers: they connect systems, move data, and take actions with delegated authority. Whether you call them “automations,” “workflows,” or “agents,” the governance question is the same:
Who can cause actions to occur under a given identity, and can you prove who did what?
In this model, credential ownership (who created the credential) can diverge from credential control (who can actually use it). That gap is where audit and accountability get blurry.
Takeaway
In n8n, credentials can be made available through:
- Explicit sharing by the credential owner
- Implicit availability within a project
- Implicit availability to instance administrators across personal projects
While n8n documents that admins can view and share credentials, it does not explicitly document that admins can execute workflows using unshared personal credentials and act under another user’s identity.
Organizations operating n8n should treat credential storage and OAuth authorization as instance-level trust decisions, and communicate that clearly to users.
This paper describes behavior, not intent. It clarifies where credential control actually resides.
Agentic governance with Linx
Most IAM teams already have a set of routines that work: access reviews, ownership assignment, least privilege, and remediation. Linx incorporates agentic identities into the same platform you use to secure and govern human and non-human identities across SaaS, cloud, and on-prem applications. That keeps visibility and governance consistent, even as identity types expand.
Read more about it here: Agentic identity discovery and governance with Linx

Maximizing Your NIST Score: The CISO’s Guide to Mastering Identity and Access Management
The NIST Cybersecurity Framework (CSF) is a critical tool for CISOs aiming to create a resilient cybersecurity posture. A high NIST score reflects a mature security program that can effectively defend against modern threats. Identity and Access Management (IAM) is central to achieving this, aligning directly with the PR.AC (Access Control) category.
This guide outlines actionable steps to enhance IAM practices and highlights how Linx Security’s platform helps organizations optimize their IAM strategy to support a high NIST score.
Step 1: Centralize Identity Management (PR.AC-1)
Managing user and system identities is fundamental to IAM maturity. Centralization is the first step toward achieving consistent and scalable identity governance and administration. This involves unifying identity data across SaaS applications, cloud platforms, and on-premises systems to provide a single source of truth.
How Linx Security Helps: Linx Security simplifies identity management by consolidating identity data from diverse sources into a unified platform. This ensures you can:
- Gain full visibility into all identities and credentials, reducing the risk of shadow IT.
- Automate identity lifecycle processes like provisioning and deprovisioning, eliminating delays and errors.
- Leverage AI-driven analytics to flag anomalies, such as dormant accounts suddenly being reactivated or roles exceeding standard permissions.
Step 2: Tighten Physical Access Controls (PR.AC-2)
Physical access control systems, such as biometric scanners or badge systems, must be integrated with digital identity systems to ensure consistency across physical and digital domains.
How Linx Security Helps: While Linx Security doesn’t provide physical security solutions directly, our platform integrates seamlessly with systems that do. By syncing physical access changes with identity policies, you maintain real-time alignment between on-site and digital access.
Step 3: Strengthen Remote Access (PR.AC-3)
Remote work introduces significant challenges for secure access. Enforcing robust authentication mechanisms and continuously monitoring remote sessions are critical to preventing breaches.
How Linx Security Helps: Linx Security’s adaptive Multi-Factor Authentication (MFA) strengthens remote access security by dynamically adjusting authentication requirements based on contextual risk factors such as device type, location, and time of access. Additionally, our platform enforces zero-trust principles by continuously validating user and device trust during remote sessions.
Step 4: Enforce Least Privilege (PR.AC-4)
Enforcing the principle of least privilege minimizes the risk of unauthorized access and limits the potential impact of insider threats or compromised accounts.
How Linx Security Helps: Linx Security automates access reviews and policy enforcement, ensuring users only have the permissions they need:
- Just-in-time (JIT) access provisioning eliminates standing privileges by granting temporary access for specific tasks.
- Intuitive dashboards streamline periodic access reviews, enabling stakeholders to quickly identify and address over-provisioned accounts.
- Privileged session monitoring captures detailed activity logs, allowing for post-incident analysis and proactive risk management.
Step 5: Secure Network Integrity (PR.AC-5)
Access control must extend to the network layer to prevent lateral movement and unauthorized access to critical systems.
How Linx Security Helps: Linx Security enforces access policies that align with segmented network zones. By combining role-based access controls (RBAC) with AI-driven monitoring, our platform ensures only authorized users interact with sensitive network segments. Suspicious behaviors—like repeated access attempts or unusual resource requests—are flagged in real time.
Step 6: Limit Access to Authorized Users, Processes, and Devices (PR.AC-6)
IAM strategies must address not only user access but also device and process-level access.
How Linx Security Helps: Our platform ensures access is limited to pre-registered, compliant devices by integrating with endpoint management tools. Behavioral analytics further enhance security by evaluating access at the process level and alerting administrators to deviations from normal activity patterns.
Step 7: Authenticate All Users, Devices, and Systems (PR.AC-7)
Authentication is foundational to secure access. Continuous authentication mechanisms are especially important in high-risk environments.
How Linx Security Helps: Linx Security supports modern authentication frameworks, including passwordless and biometric methods. Additionally, our platform integrates certificate-based authentication for devices, ensuring only trusted endpoints can access sensitive systems. With continuous authentication, users are validated throughout their sessions based on behavioral and environmental data.
Beyond the Basics: Advanced IAM for Maximum NIST Scores
Maximizing your NIST score often requires moving beyond foundational practices. Linx Security equips organizations with advanced IAM capabilities that include:
- AI-Powered Insights: Identify and mitigate risks in real time with machine learning-driven analytics.
- Support for Non-Human Identities: Secure machine accounts, APIs, and IoT devices with robust identity governance.
- Seamless Integration: Connect with your existing security stack for streamlined operations.
The Value of a High NIST Score
Achieving and maintaining a high NIST score signals a proactive and resilient cybersecurity program. With IAM as its backbone, you not only protect your organization against current threats but also prepare for future challenges. Linx Security empowers CISOs to align IAM practices with NIST CSF standards and achieve measurable improvements in their security posture.
How Linx Security Can Help
Linx Security provides the tools and expertise to help your organization achieve IAM excellence. Whether you’re managing identities across hybrid environments, enforcing zero-trust principles, or streamlining access reviews, we’re here to support your journey.
Contact us today to get started.
Visibility without action is like an expensive car without a motor—impressive but ultimately useless. In today’s rapidly evolving digital landscape, managing identity and access is one of the most critical challenges organizations face. With employees, contractors, and systems accessing a mix of SaaS platforms, on-premises infrastructure, and multi-cloud environments, ensuring that access is appropriate, compliant, and secure is no small feat. While many organizations excel at detecting risks like over-provisioned accounts or dormant entitlements, far fewer are equipped to address these vulnerabilities effectively and in real time.
This is where remediation takes center stage. Effective identity governance and security aren’t just about having policies in place or identifying risks—they hinge on the ability to take swift, decisive action. Without remediation, gaps between governance policies and security enforcement widen, exposing organizations to threats, inefficiencies, and compliance violations.
Why Real-Time Remediation is Vital
At the heart of identity governance lies the ability to ensure that access policies are consistently enforced across users, roles, and systems. Security, on the other hand, seeks to minimize risk by addressing vulnerabilities such as privilege sprawl or dormant accounts. These two disciplines—governance and security—must work in unison. Real-time remediation acts as the bridge, enabling organizations to move seamlessly from policy to action and from detection to resolution.
Governance and Security: A Unified Imperative
Governance frameworks such as ISO 27001, GDPR, NYDFS, and SOX require organizations to define and enforce strict access policies. Yet, without security mechanisms to ensure compliance, these frameworks remain aspirational. Security initiatives like least-privilege enforcement rely on governance to define appropriate access levels but require real-time remediation to maintain them dynamically.
A global retail company discovered during a compliance audit that 12% of employees retained access to inventory systems long after transitioning to non-operational roles. While governance frameworks mandated role-based access policies, the company’s manual processes delayed remediation, leaving these permissions active for months. By integrating Linx Security’s automated workflows, the organization ensured immediate adjustments to permissions during employee transitions, maintaining both compliance and security standards.
Real-Time Remediation in Action
1. Enforcing Least Privilege at Scale
Least-privilege access is a cornerstone of both governance and security, but maintaining it in dynamic, large-scale environments is a challenge. Without real-time remediation, privilege drift—where users accumulate excessive permissions over time—can undermine governance principles and expand the attack surface.
Financial institutions implement Linx Security to enforce least privilege dynamically. When a project-based contractor is granted elevated permissions to work on a trading system, Linx Security’s time-bound access controls automatically revoke these permissions upon project completion. This approach ensures compliance with the institution’s internal governance policies while minimizing risk exposure.
2. Automating the Joiner-Mover-Leaver (JML) Lifecycle
Managing access during the JML lifecycle is critical to ensuring governance and security. Onboarding (joiner), role transitions (mover), and offboarding (leaver) events are common sources of access mismanagement, leading to dormant accounts or lingering permissions.
Healthcare providers face challenges adhering to HIPAA regulations due to delays in deprovisioning accounts after employee departures. With Linx Security’s integration into HR and IT systems, offboarding triggers now initiate immediate access revocation for all associated systems, from electronic health records to billing platforms. Additionally, when employees move roles, their permissions are adjusted to align with their new responsibilities, preventing access overlap.
3. Continuous Monitoring and Policy Alignment
Identity governance isn’t static; it requires continuous monitoring and realignment of access with evolving policies and roles. Automated workflows for detecting and remediating anomalies ensure governance and security remain tightly coupled.
One of our SaaS company partners using Linx Security identified excessive permissions in its engineering department. Some developers had access to sensitive customer data that was not relevant to their roles. Linx’s platform flagged the misalignment and initiated an automated identity risk remediation workflow, revoking inappropriate access and maintaining an audit trail to support compliance efforts during external audits.
How Real-Time Remediation Enhances Security and Governance
Real-time remediation doesn’t just address immediate risks—it strengthens the foundation of an organization’s identity governance and security strategy. Here’s how:
- Dynamic Policy Enforcement: By aligning access with roles, functions, and organizational policies in real time, organizations ensure continuous compliance with governance frameworks.
- Minimized Attack Surface: Dormant accounts and privilege sprawl are proactively addressed, reducing the number of exploitable entry points for attackers.
- Audit-Ready Transparency: Automated workflows maintain detailed logs of every action, simplifying compliance with regulations like GDPR, HIPAA, and SOX.
- Risk-Based Prioritization: Linx Security enables organizations to focus remediation efforts on the most critical risks, such as administrative privilege escalations or unauthorized lateral movement.
A Holistic Approach to Governance and Security
The success of identity governance and security depends on their ability to work together seamlessly. Governance provides the blueprint, defining what access is appropriate, while security ensures these policies are enforced dynamically. Real-time remediation bridges the gap by transforming policies into action, reducing risk, and enabling continuous compliance.
At Linx Security, we specialize in unifying governance and security through proactive, automated remediation. Our platform empowers organizations to enforce policies, reduce vulnerabilities, and adapt to the complexities of modern identity governance and administration with confidence.
Conclusion: From Policy and Risk to Action
Identity governance and security are no longer optional in today’s hyper-connected enterprise environments—they are fundamental. But governance without action and security without policy alignment are incomplete. Real-time remediation is the critical element that unites these disciplines, allowing organizations to detect risks, take action, and maintain compliance in an ever-changing landscape.
If you’re ready to elevate your identity governance and security strategy, Linx Security is here to help. Together, we can close the governance-security gap and build a more secure future.

The Urgency of PCI DSS 4.0 Compliance: Why Access Management is Crucial
With the imminent arrival of PCI DSS 4.0, organizations handling payment card data are facing a significant shift in compliance requirements. This new version, expanding from 370 to over 500 requirements, reflects a comprehensive update to enhance data security in an evolving threat landscape. As we approach the March 2025 deadline, there's an urgent need to understand and implement these changes, particularly in the realm of access management.
Why PCI DSS 4.0 Puts Access Management in the Spotlight
Access management has long been a cornerstone of data security, but PCI DSS 4.0 elevates its importance significantly. The updated standard introduces stricter requirements around:
- Least Privilege Access (Requirement 7): Mandating that users have access only to the information necessary for their role, reduces the risk of data exposure.
- Multi-Factor Authentication (Requirement 8.3): Requiring MFA for non-console access to the cardholder data environment, adding a crucial layer of security against unauthorized access.
- Enhanced Logging and Monitoring (Requirement 10): Strengthening the ability to detect and respond to unauthorized access through more detailed logging and continuous monitoring.
These changes reflect a deeper understanding that securing access to sensitive data is not just about external threats but also about managing and mitigating internal risks. Unauthorized access—whether due to malicious intent or simple oversight—poses one of the greatest vulnerabilities to an organization's data security.
The Imperative of Robust Access Management
The emphasis on access management in PCI DSS 4.0 is not merely a regulatory box to tick; it's a critical component of an organization's overall security strategy. Here's why it's essential:
- Evolving Threats: As cyber threats become more sophisticated, attackers are increasingly targeting user credentials as a way into systems. Effective access management, including practices like least privilege and MFA, is crucial in defending against these threats.
- Complex Compliance Landscape: With the new standard introducing more granular requirements, maintaining compliance can be complex. Proper access management provides a structured way to enforce consistent policies across all user groups and systems.
- Reducing Insider Risk: Not all threats come from outside. By enforcing strict access controls and regularly reviewing permissions, organizations can mitigate the risks posed by insider threats, whether malicious or accidental.
Key Strategies for Effective Access Management
To align with PCI DSS 4.0 and strengthen security, organizations should focus on implementing key access management strategies:
- Automated Access Control Systems: Automating the provisioning and de-provisioning of user access ensures that permissions are always up-to-date and reflect the principle of least privilege. This automation reduces the risk of unnecessary access lingering in the system. Solutions that integrate seamlessly with existing infrastructures can make this process more efficient and less prone to human error.
- Implementing Multi-Factor Authentication (MFA): MFA is a critical component in protecting sensitive environments. By requiring additional verification steps, MFA significantly reduces the likelihood of unauthorized access even if credentials are compromised. Implementing MFA in a way that is user-friendly and scalable across the organization is key to its success.
- Regular Access Reviews: Conducting periodic reviews of user access rights helps to identify and correct any discrepancies, ensuring that access permissions remain appropriate and secure over time. Leveraging tools that can automate and simplify these reviews can make ongoing compliance more manageable.
- Comprehensive Logging and Monitoring: Implementing robust logging and monitoring systems allows for the detection of suspicious activities in real-time, enabling a swift response to potential security incidents. Solutions that offer real-time alerts and detailed reporting can enhance an organization’s ability to detect and respond to threats promptly.
Preparing for the Transition to PCI DSS 4.0
With the transition deadline set for March 2024, and the introduction of new best practices required by March 2025, organizations need to act swiftly. This period presents an opportunity to not only achieve compliance but also to build a more resilient security posture.
The first step in this journey is conducting a thorough gap analysis to understand where current practices may fall short of the new requirements. From there, developing a clear roadmap for implementing enhanced access controls and other measures is crucial. Engaging with partners who deeply understand the technical and regulatory aspects of PCI DSS 4.0 can provide valuable guidance and support throughout this process.
Access Management as a Cornerstone of Security
The urgency of PCI DSS 4.0 compliance is clear, but at its core, this is about more than just adhering to a set of rules. It's about recognizing that access management is a foundational element of data security. By focusing on implementing robust access controls, organizations can better protect their data, reduce the risk of breaches, and ultimately build stronger, more secure systems.
For organizations seeking to navigate the complexities of PCI DSS 4.0, solutions that offer automated access management, MFA implementation, and continuous monitoring can make a significant difference. These tools not only help achieve compliance but also enhance the organization's overall security framework, providing peace of mind in an increasingly complex digital landscape.
If youʼre looking for expert guidance to navigate the transition to PCI DSS 4.0 and enhance your access management capabilities, contact us at Linx Security. Our team is ready to help you build a stronger, more secure future.
Sign up to get new articles & updates from the Linx team sent straight to you.




